Design and Basic Evaluation of Virtual IPv4 based CYPHONIC adapter
埋め込みコード
iframe
<iframe src="https://www.ren510.dev/slides/embed/design-and-basic-evaluation-of-virtual-ipv4-based-cyphonic-adapter/" title="Design and Basic Evaluation of Virtual IPv4 based CYPHONIC adapter" width="100%" style="aspect-ratio:1.778" frameborder="0" allow="clipboard-write" allowfullscreen></iframe>script タグ
<script defer class="ren510-slide-embed" data-slug="design-and-basic-evaluation-of-virtual-ipv4-based-cyphonic-adapter" data-ratio="1.7777777777777777" src="https://www.ren510.dev/static/slides/embed.js"></script>🤖 AI による要約 ✨
- P.1 — Title slide. "Design and Basic Evaluation of Virtual IPv4 based CYPHONIC adapter" presented at IMCIC 2022
- P.2 — Presentation outline covering network security, CYPHONIC concept, issues, objective, proposed system, evaluation, and conclusions
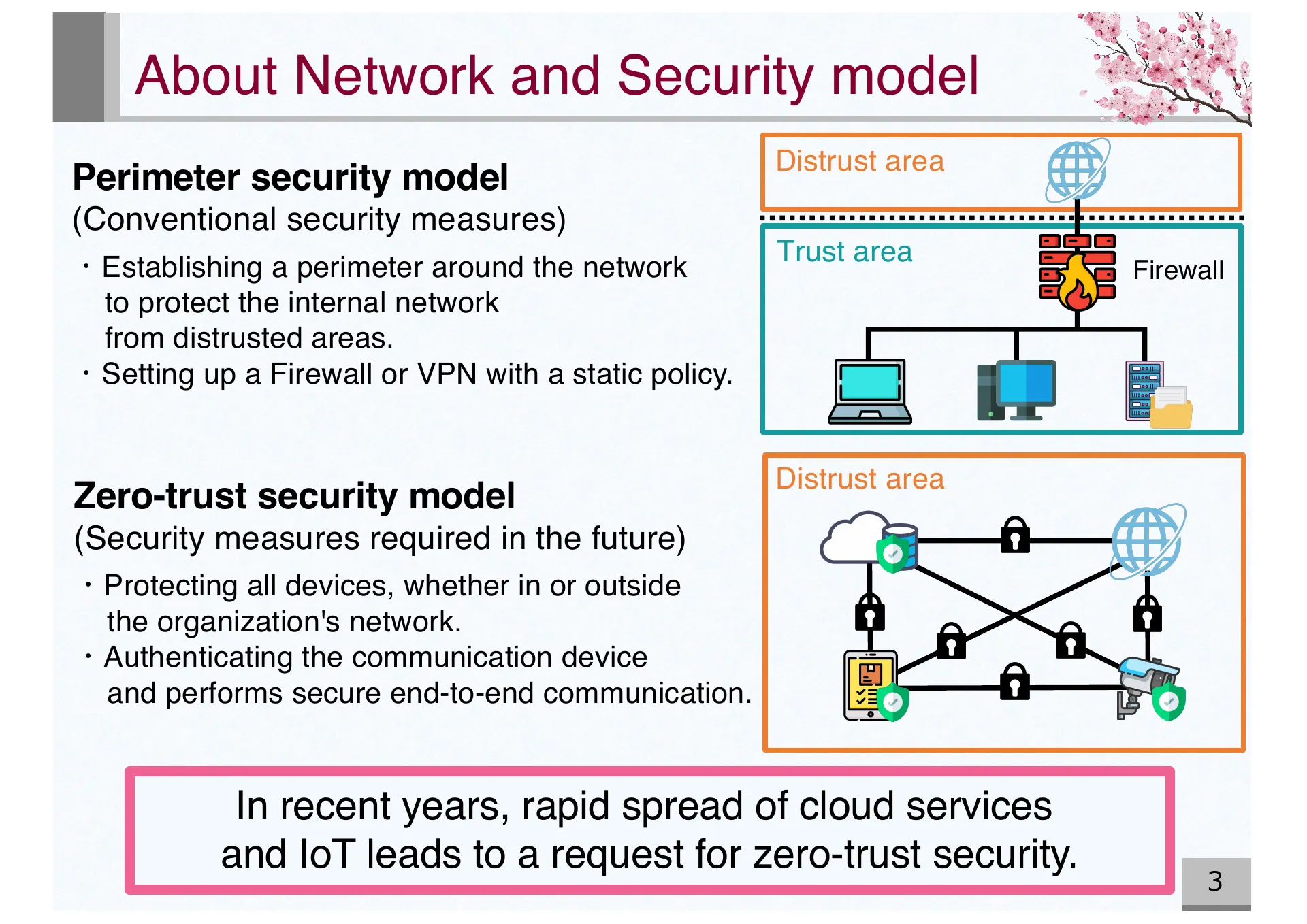
- P.3 — Comparison of perimeter security model and zero-trust security model. Cloud and IoT spread drives demand for zero-trust
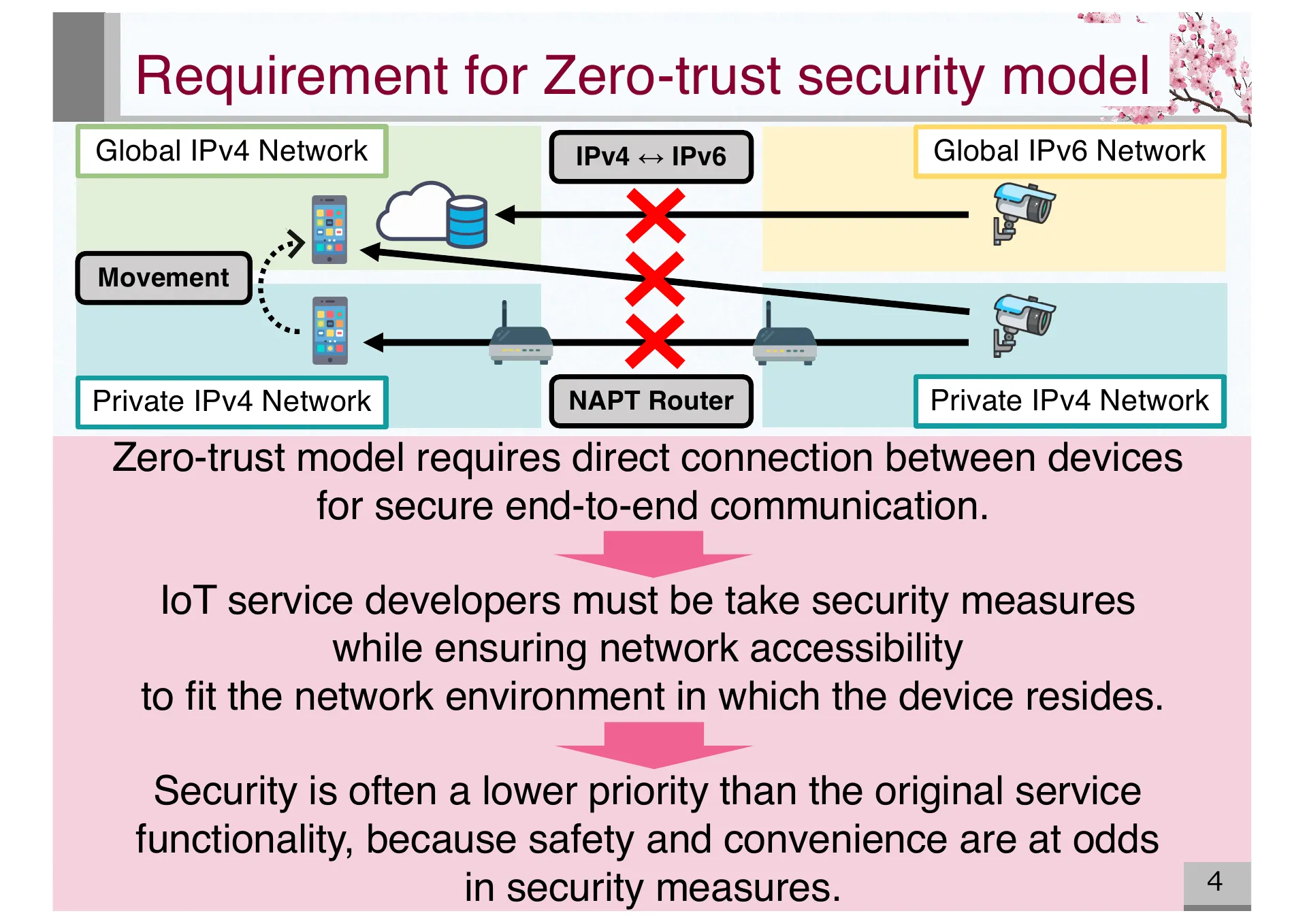
- P.4 — Requirements for zero-trust security model. Direct device connection needed for secure end-to-end communication across diverse network environments
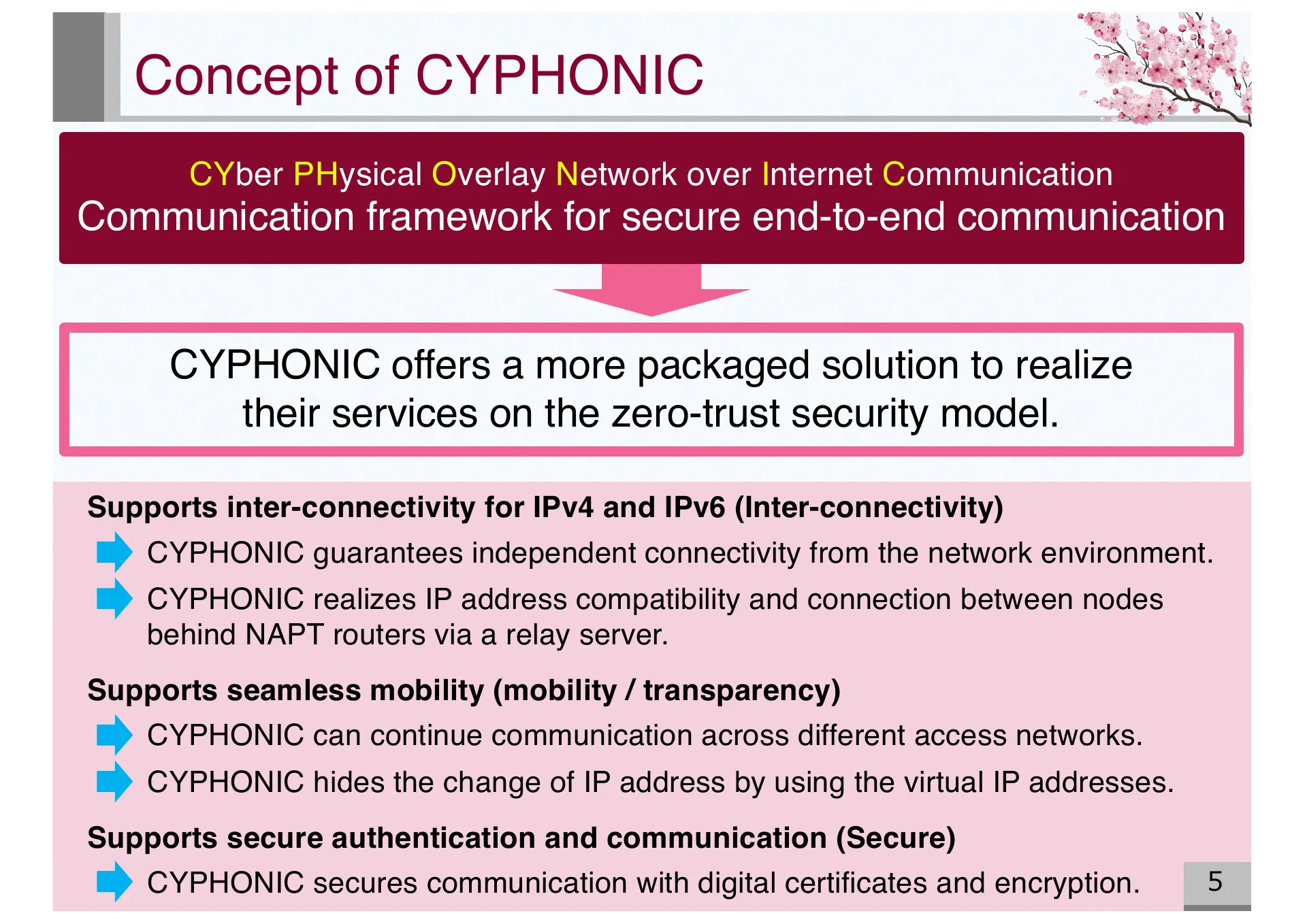
- P.5 — Concept of CYPHONIC (CYber PHysical Overlay Network over Internet Communication). Supports inter-connectivity, seamless mobility, and secure authentication
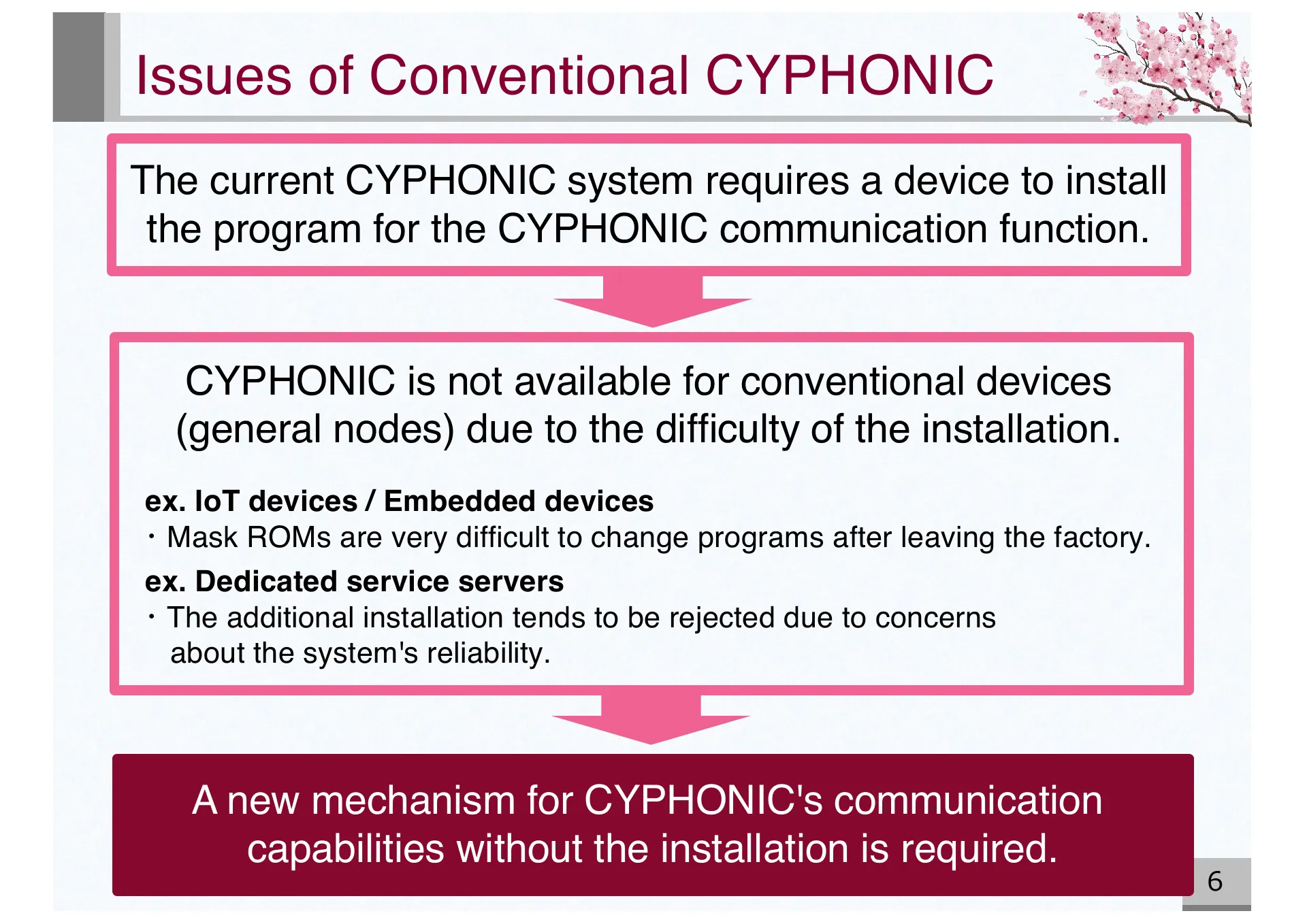
- P.6 — Issues of conventional CYPHONIC. General nodes like IoT and embedded devices cannot install CYPHONIC programs
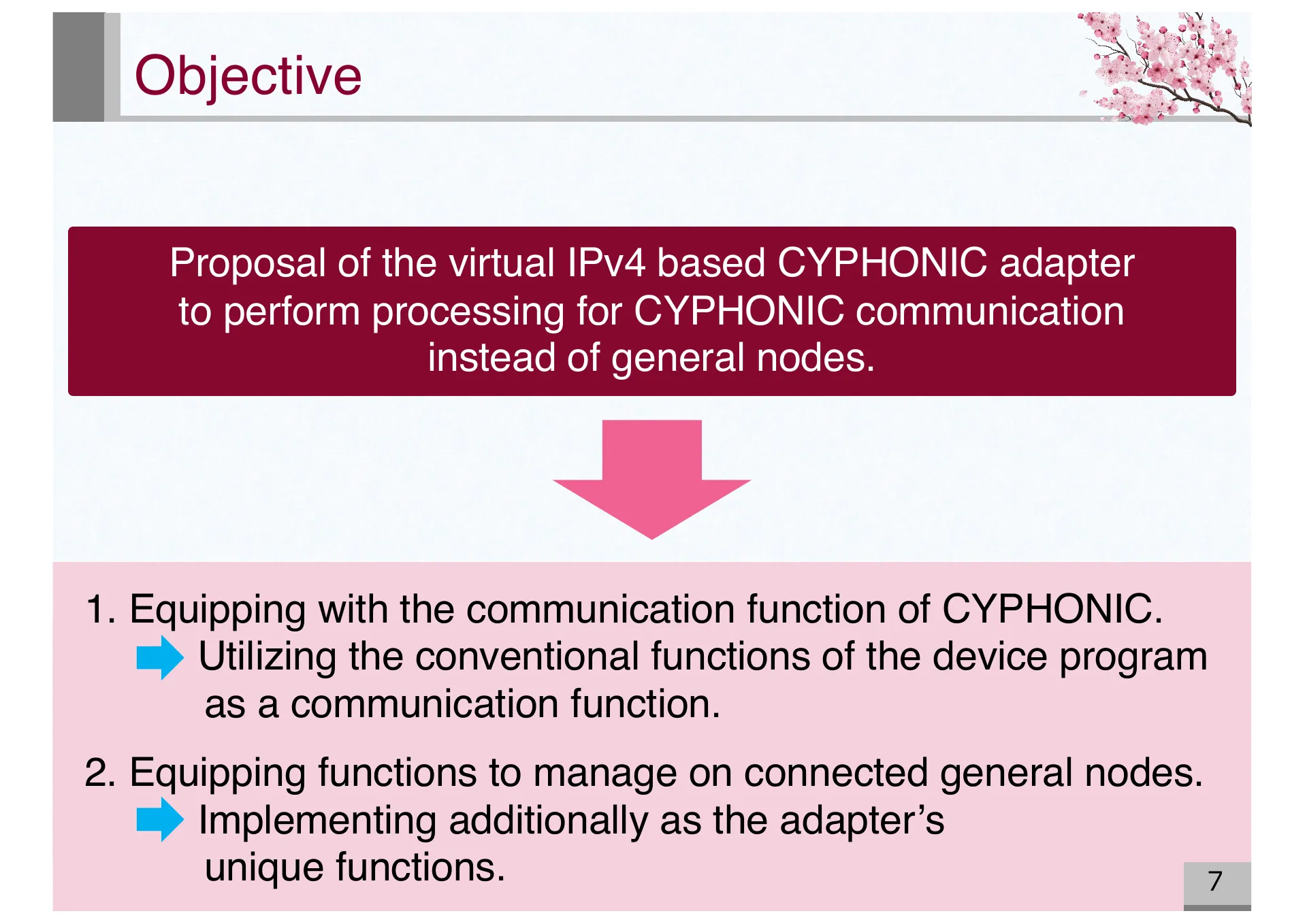
- P.7 — Objective: Proposal of virtual IPv4 based CYPHONIC adapter to perform CYPHONIC communication on behalf of general nodes
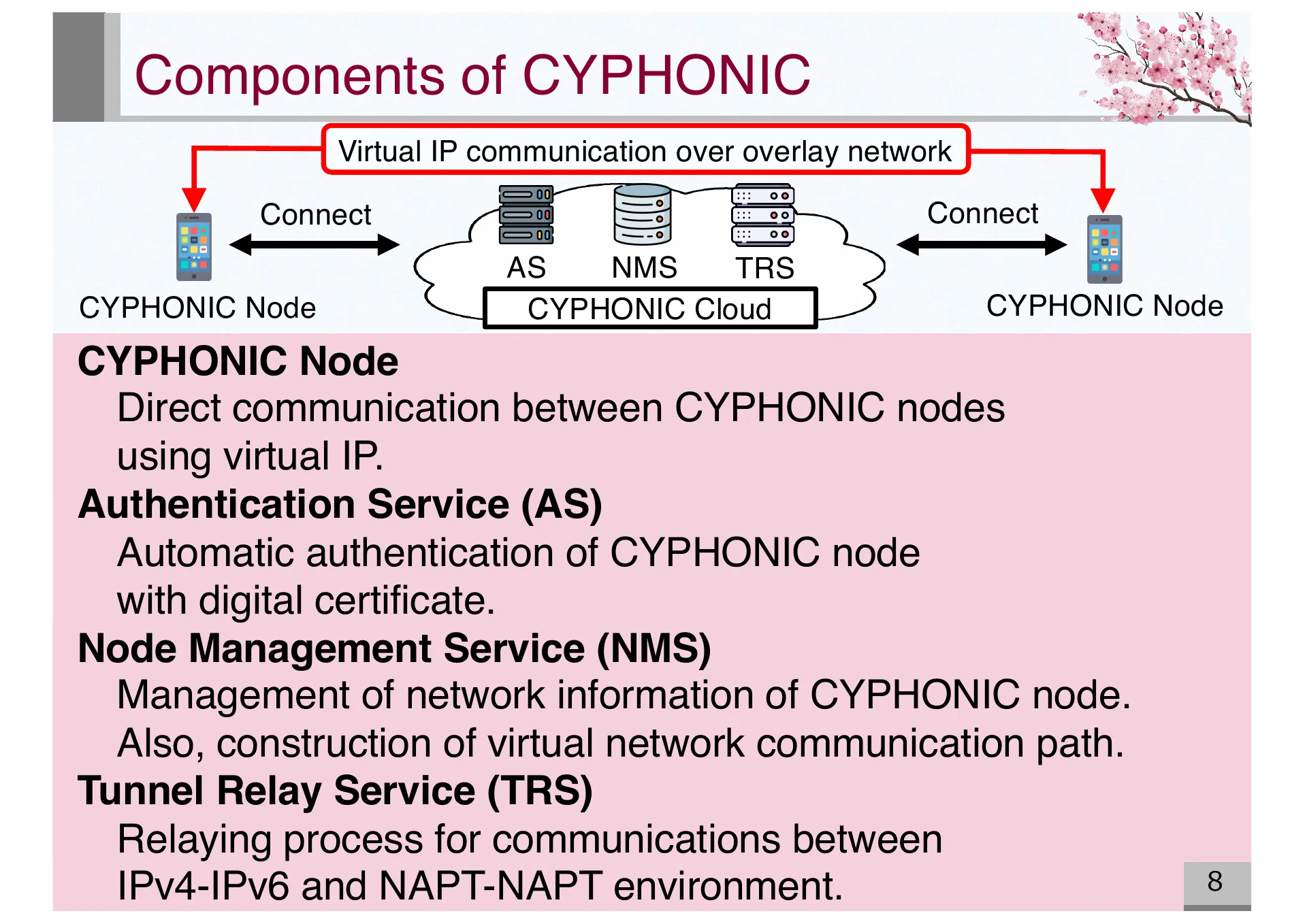
- P.8 — Components of CYPHONIC: CYPHONIC Node, Authentication Service (AS), Node Management Service (NMS), and Tunnel Relay Service (TRS)
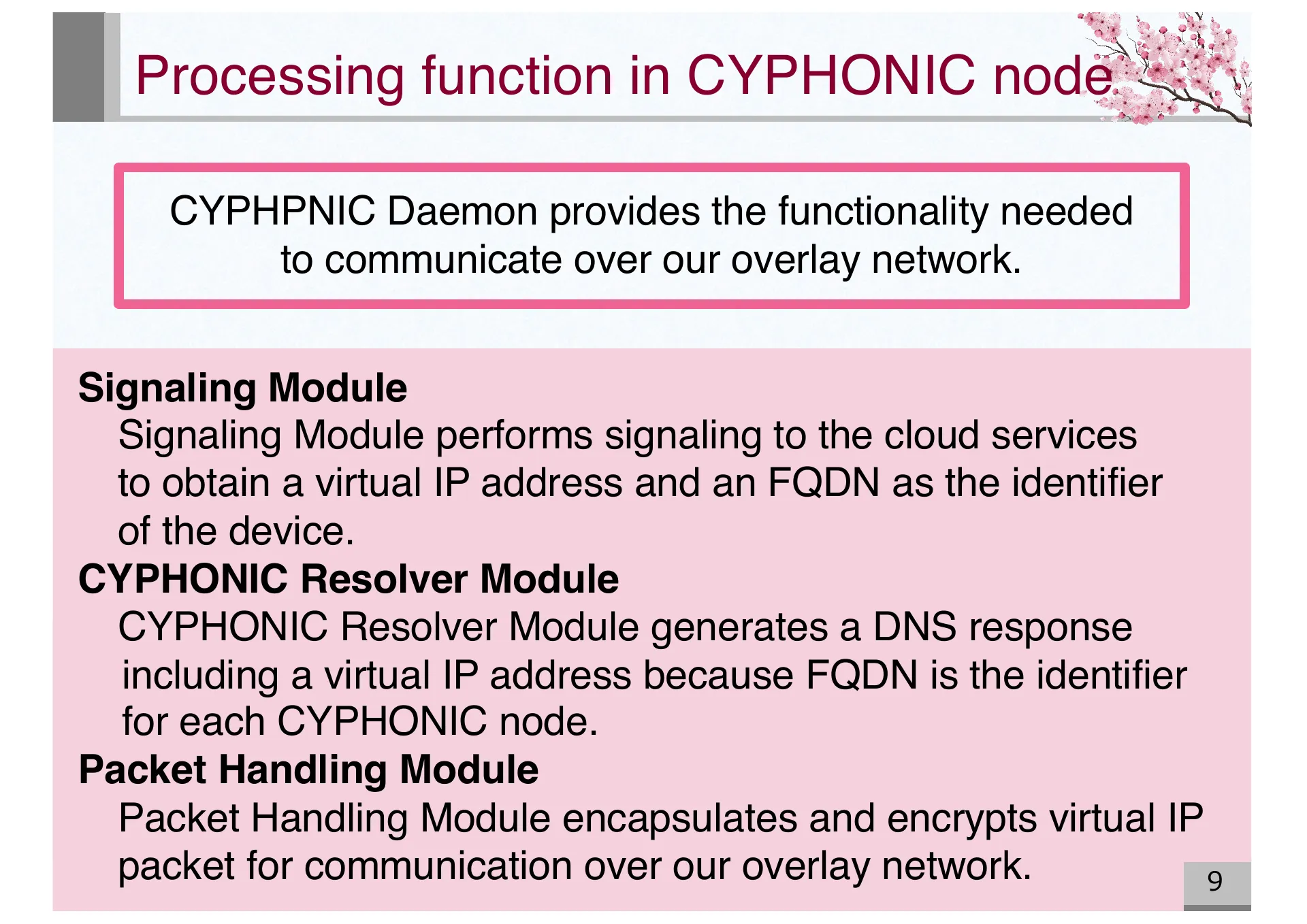
- P.9 — Processing functions in CYPHONIC node: Signaling Module, CYPHONIC Resolver Module, and Packet Handling Module
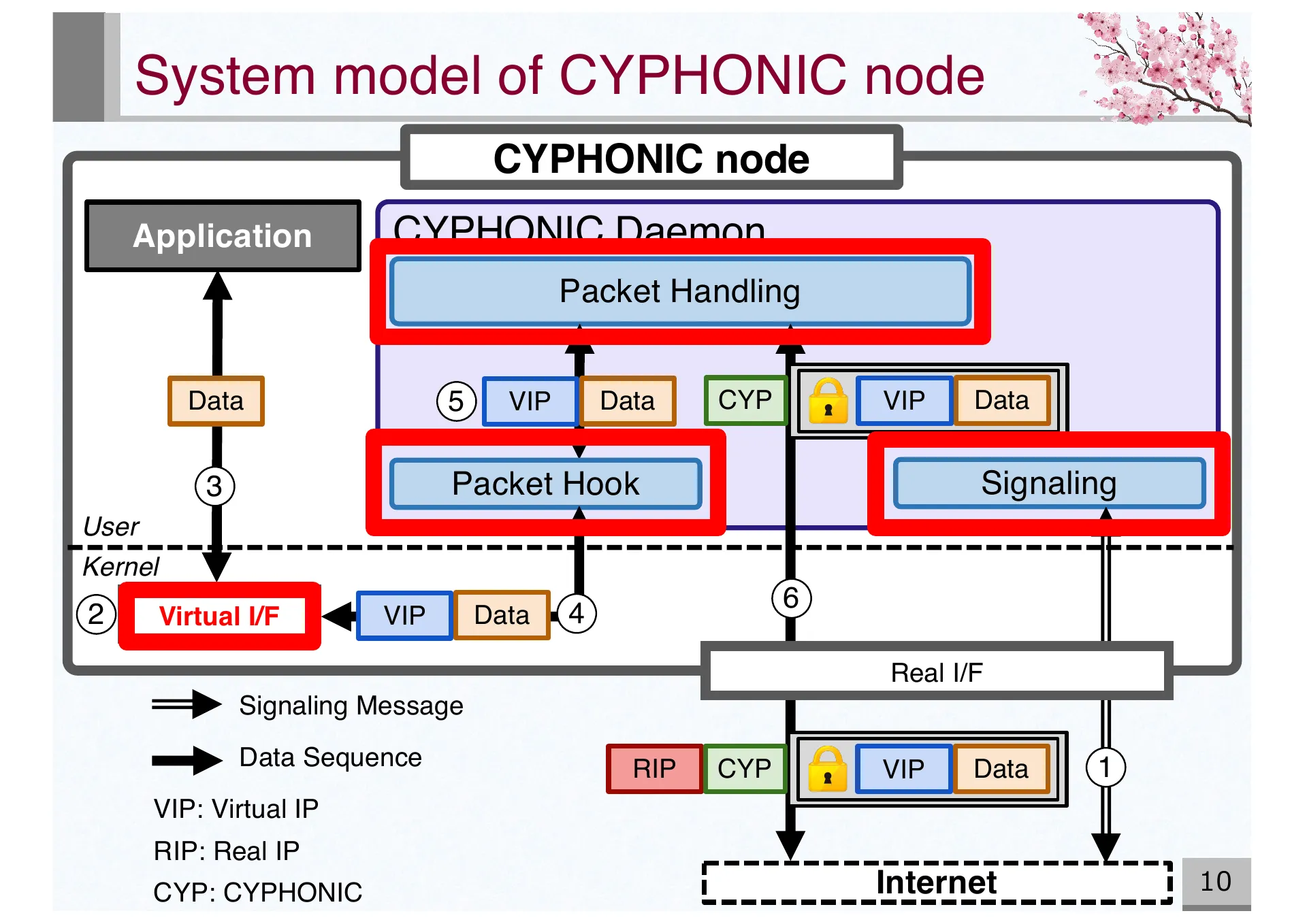
- P.10 — System model of CYPHONIC node showing data flow between application, CYPHONIC Daemon, virtual/real interfaces, and the Internet
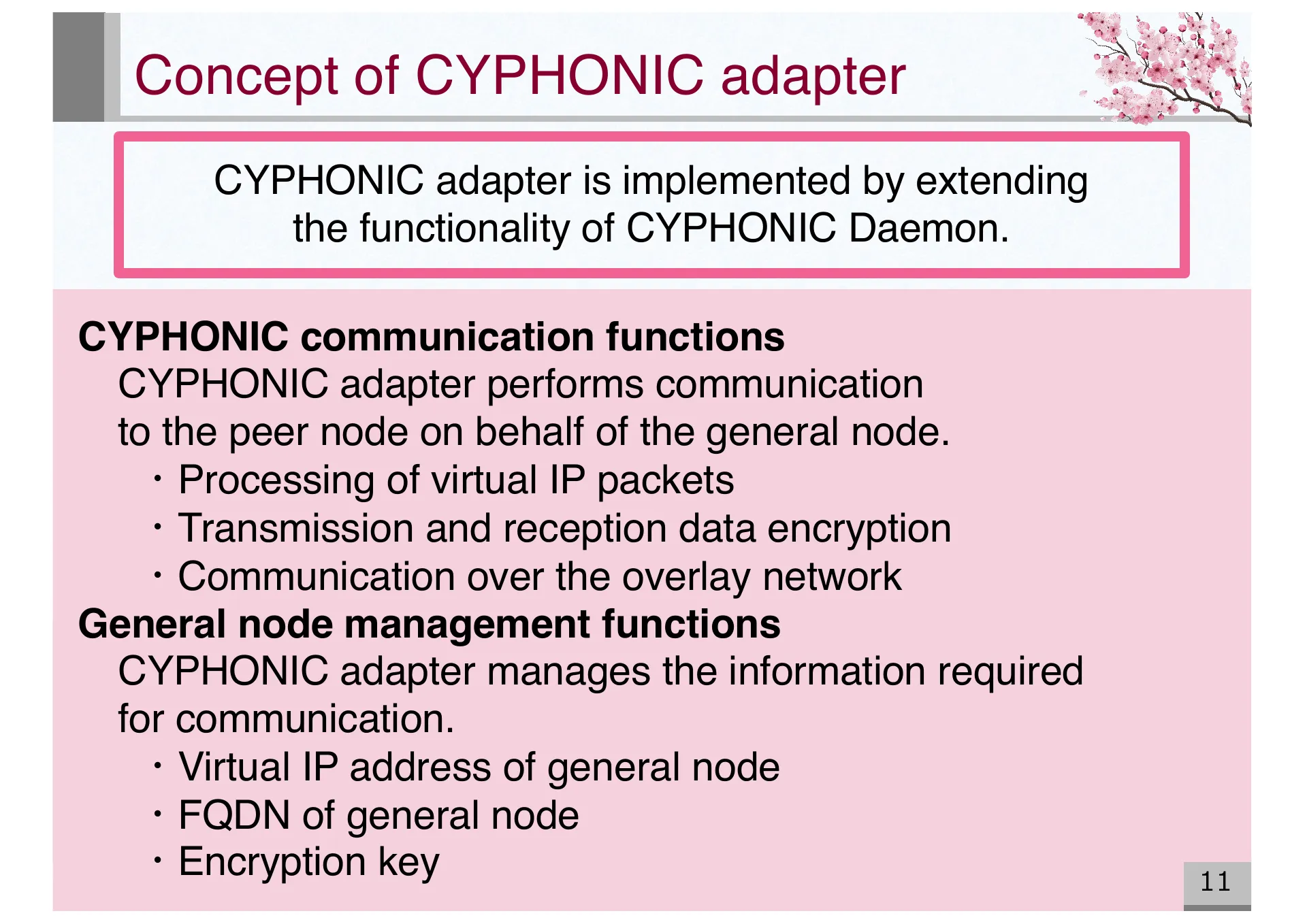
- P.11 — Concept of CYPHONIC adapter. Extends CYPHONIC Daemon to perform communication on behalf of general nodes and manage their information
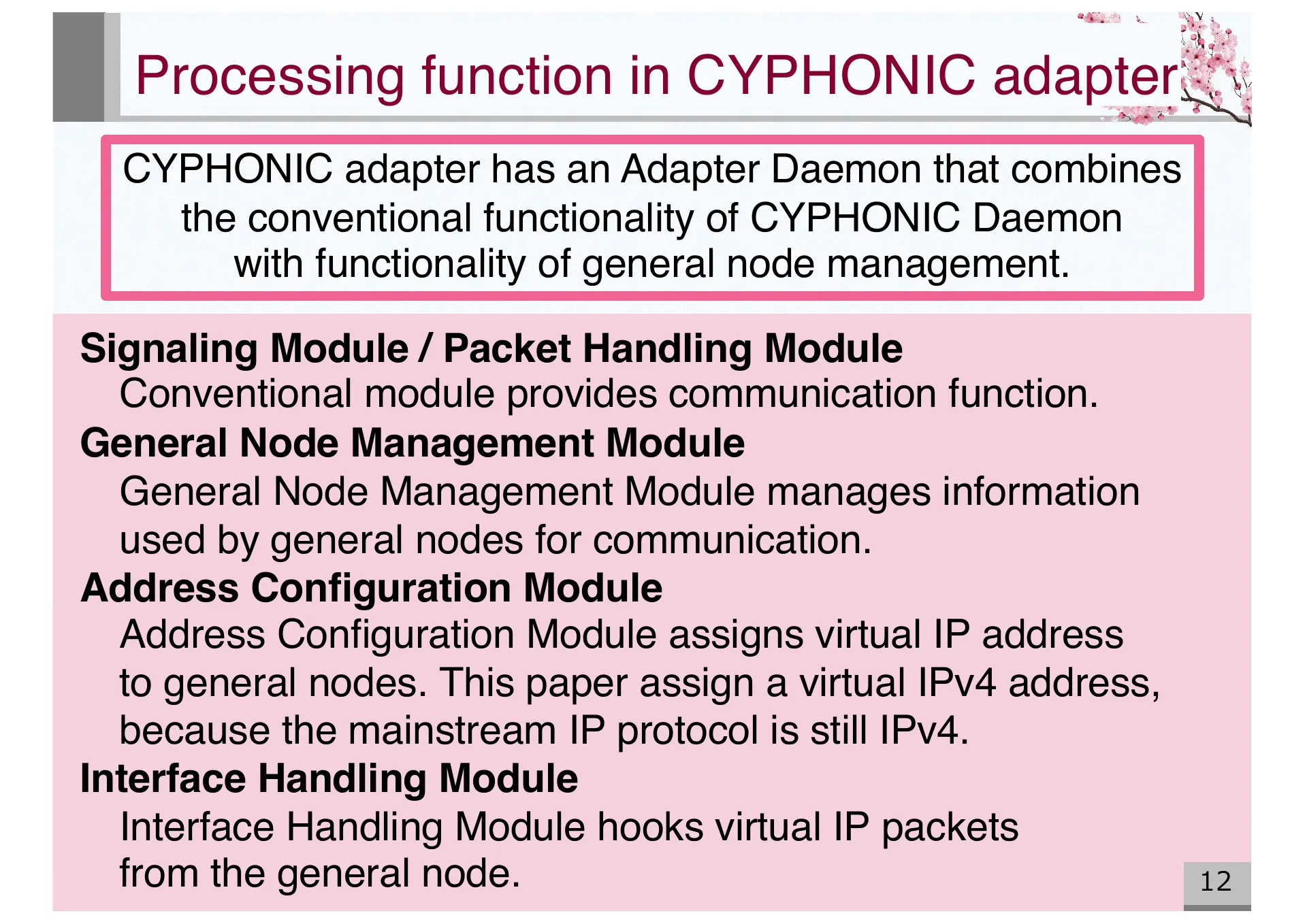
- P.12 — Processing functions in CYPHONIC adapter: Signaling, Packet Handling, General Node Management, Address Configuration, and Interface Handling Modules
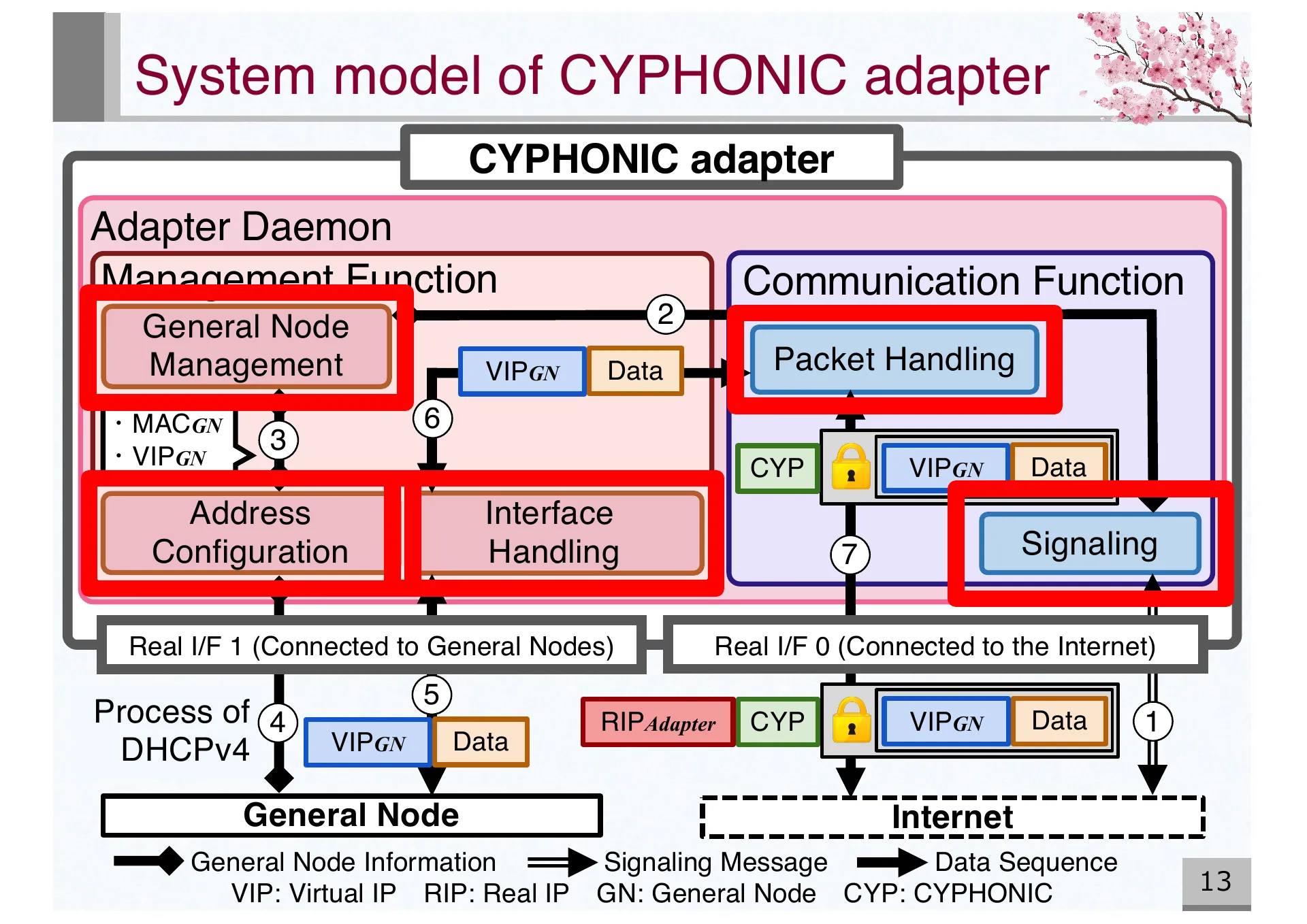
- P.13 — System model of CYPHONIC adapter showing Adapter Daemon with management and communication functions connected via two real interfaces
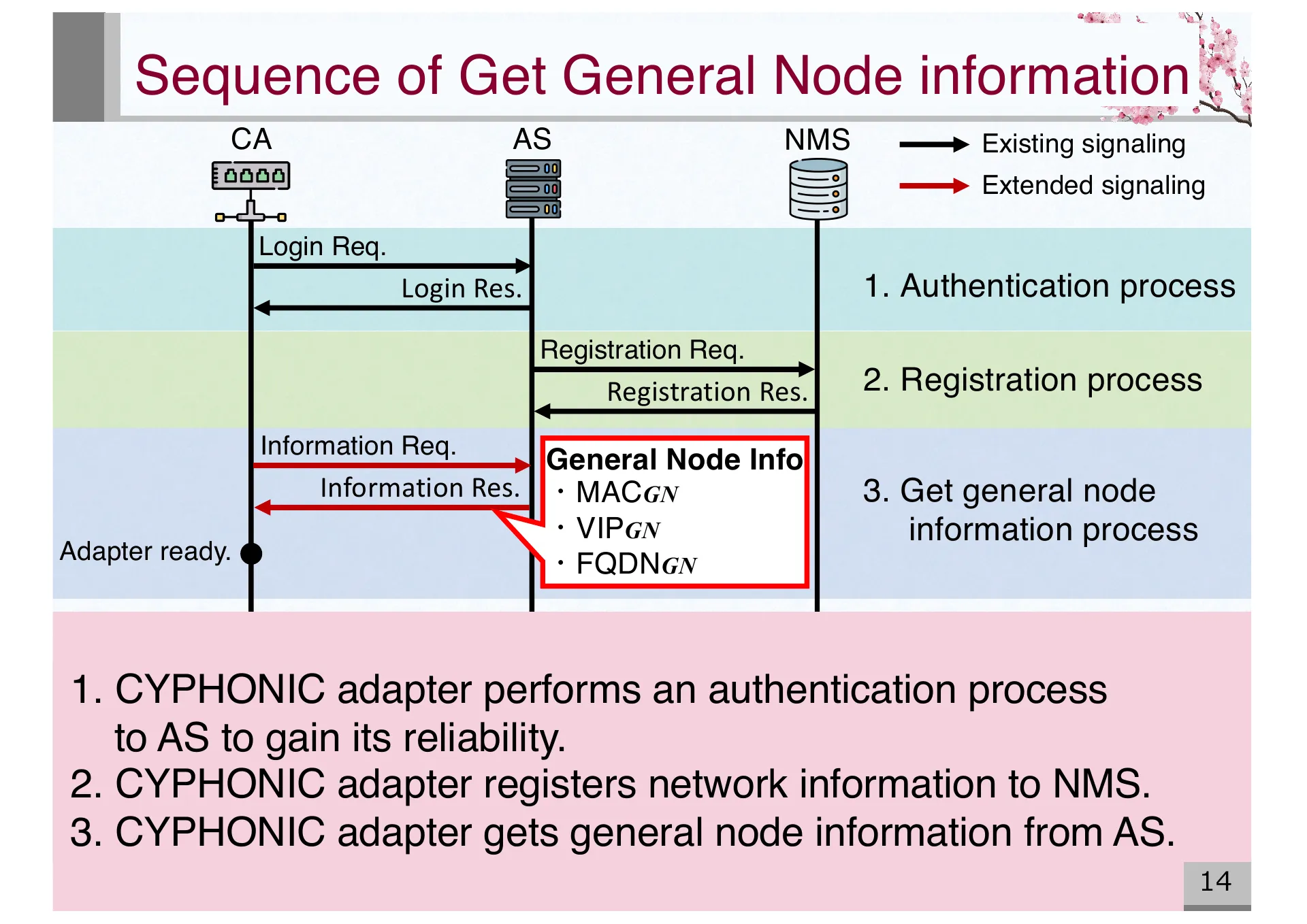
- P.14 — Sequence diagram for getting general node information: authentication, registration, and information retrieval from AS and NMS
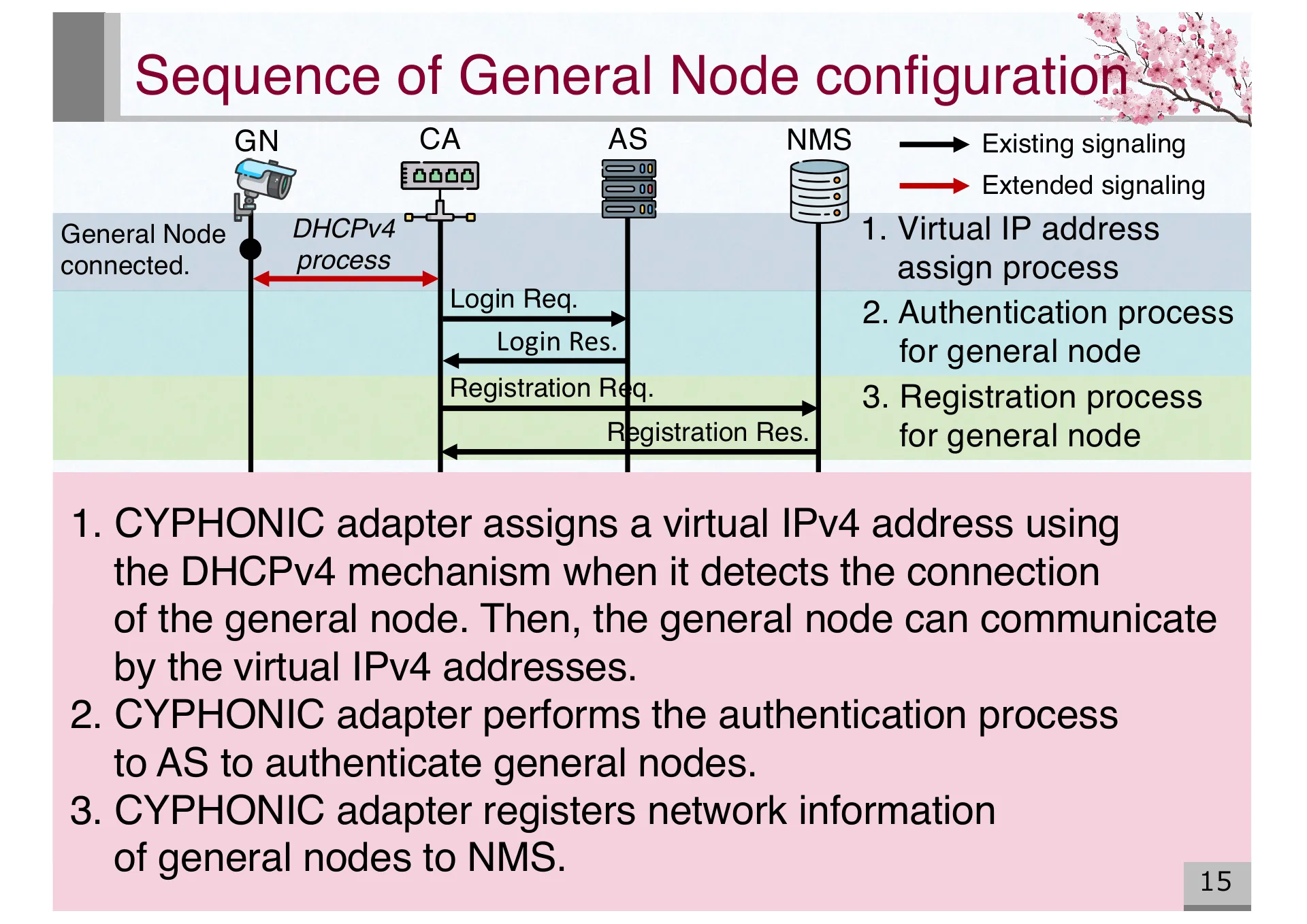
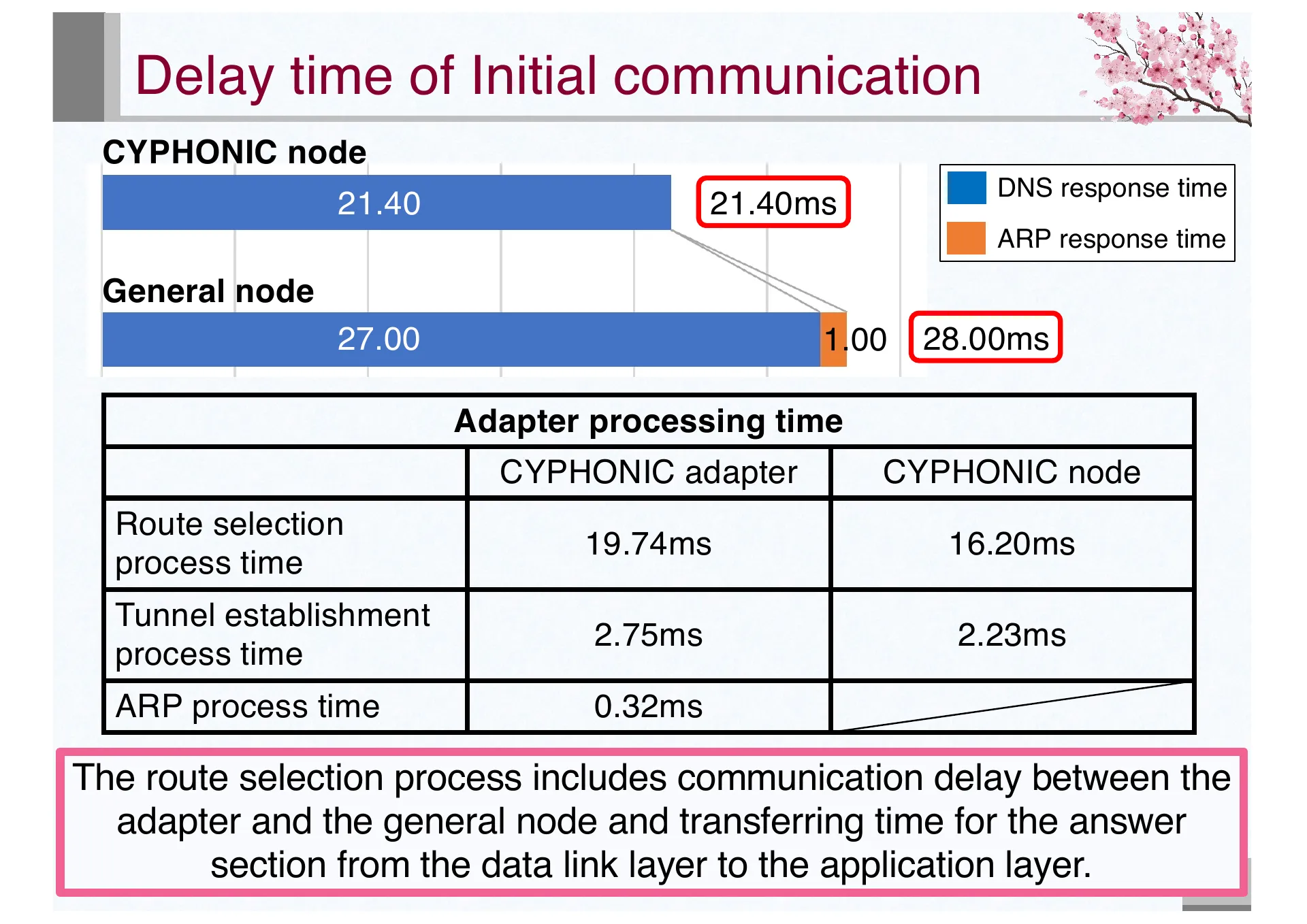
- P.15 — Sequence of general node configuration: virtual IPv4 address assignment via DHCPv4, authentication, and registration for general nodes
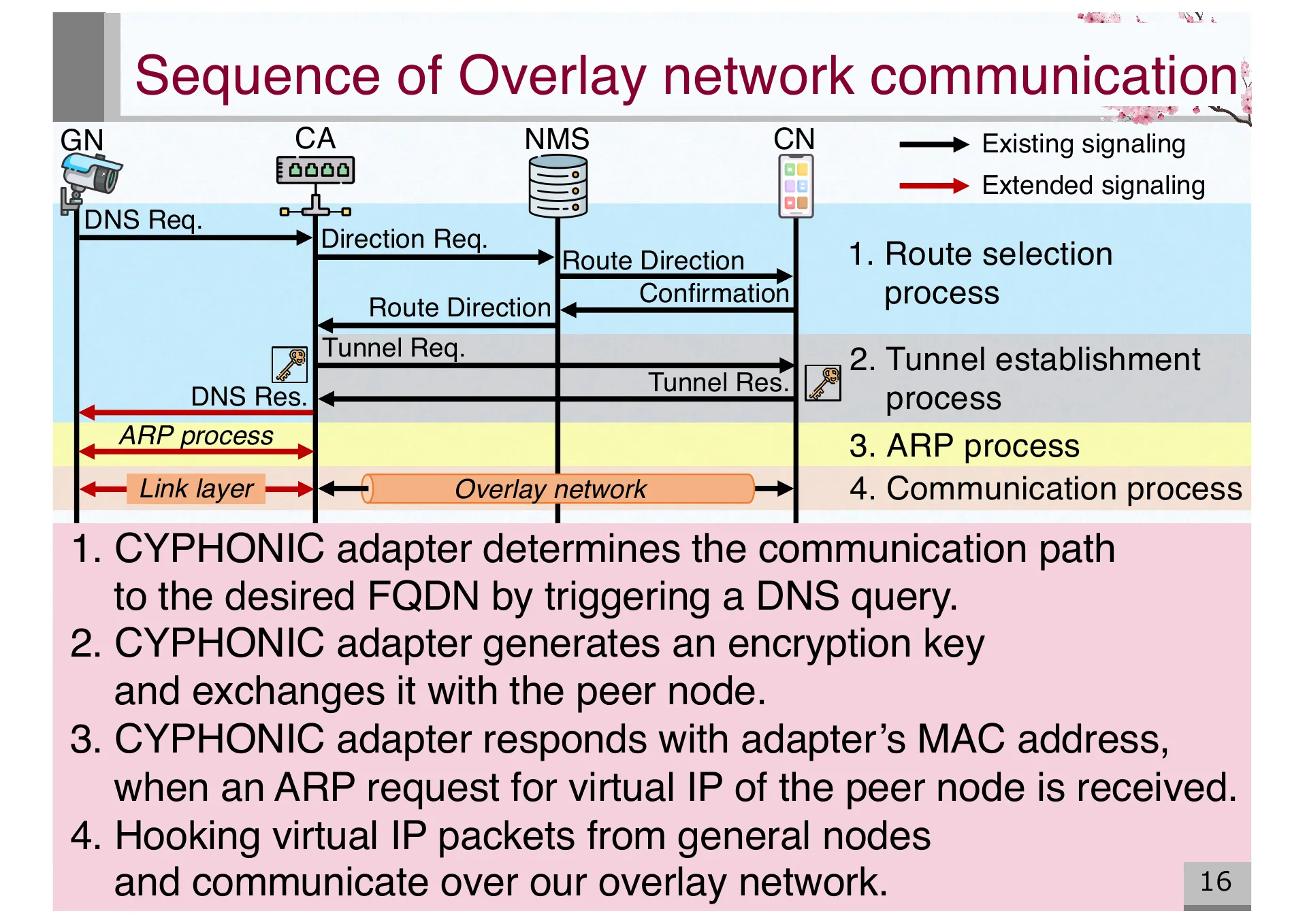
- P.16 — Sequence of overlay network communication: route selection, tunnel establishment, ARP process, and data communication
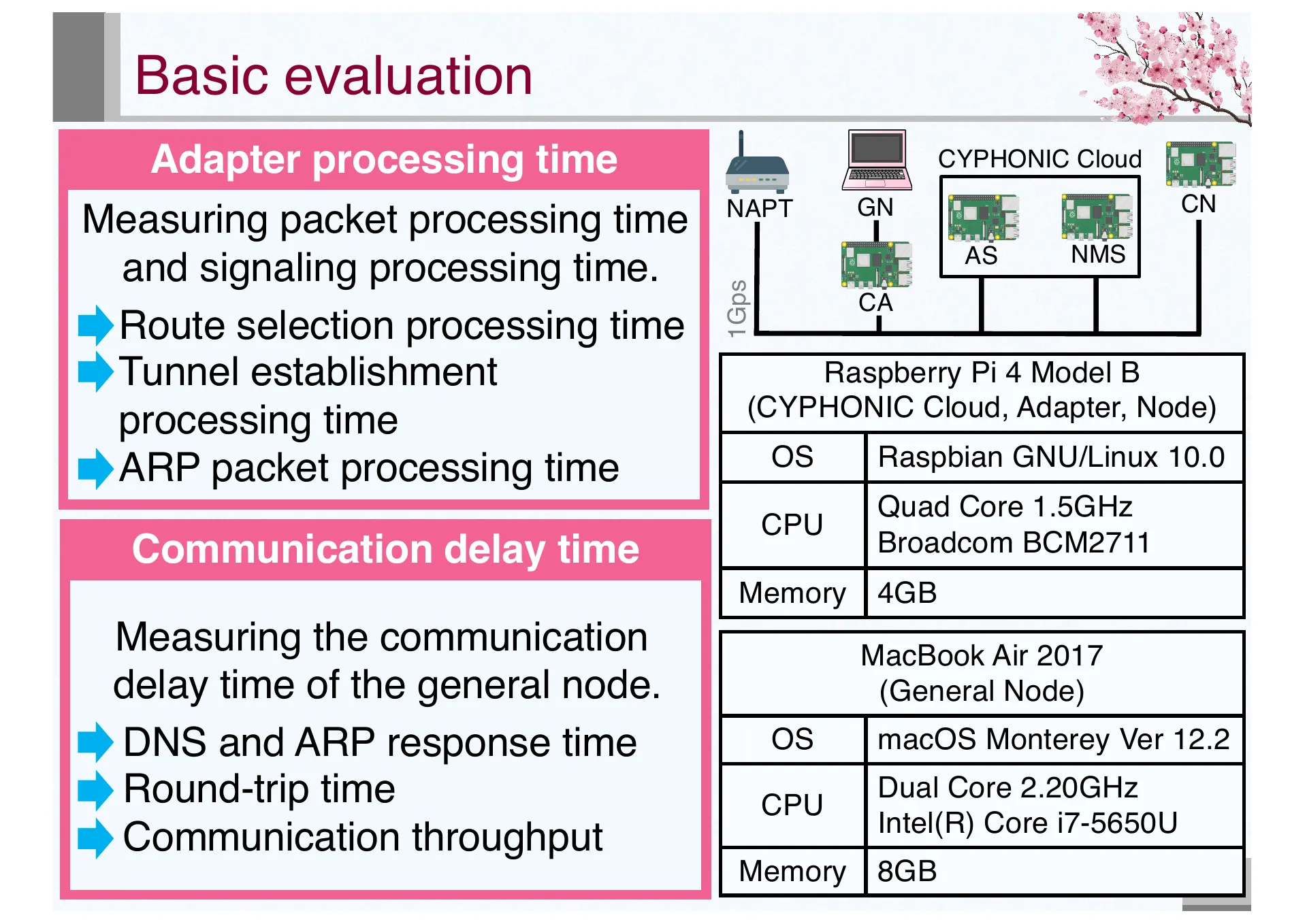
- P.17 — Basic evaluation setup. Measuring adapter processing time and communication performance using Raspberry Pi 4 and MacBook Air
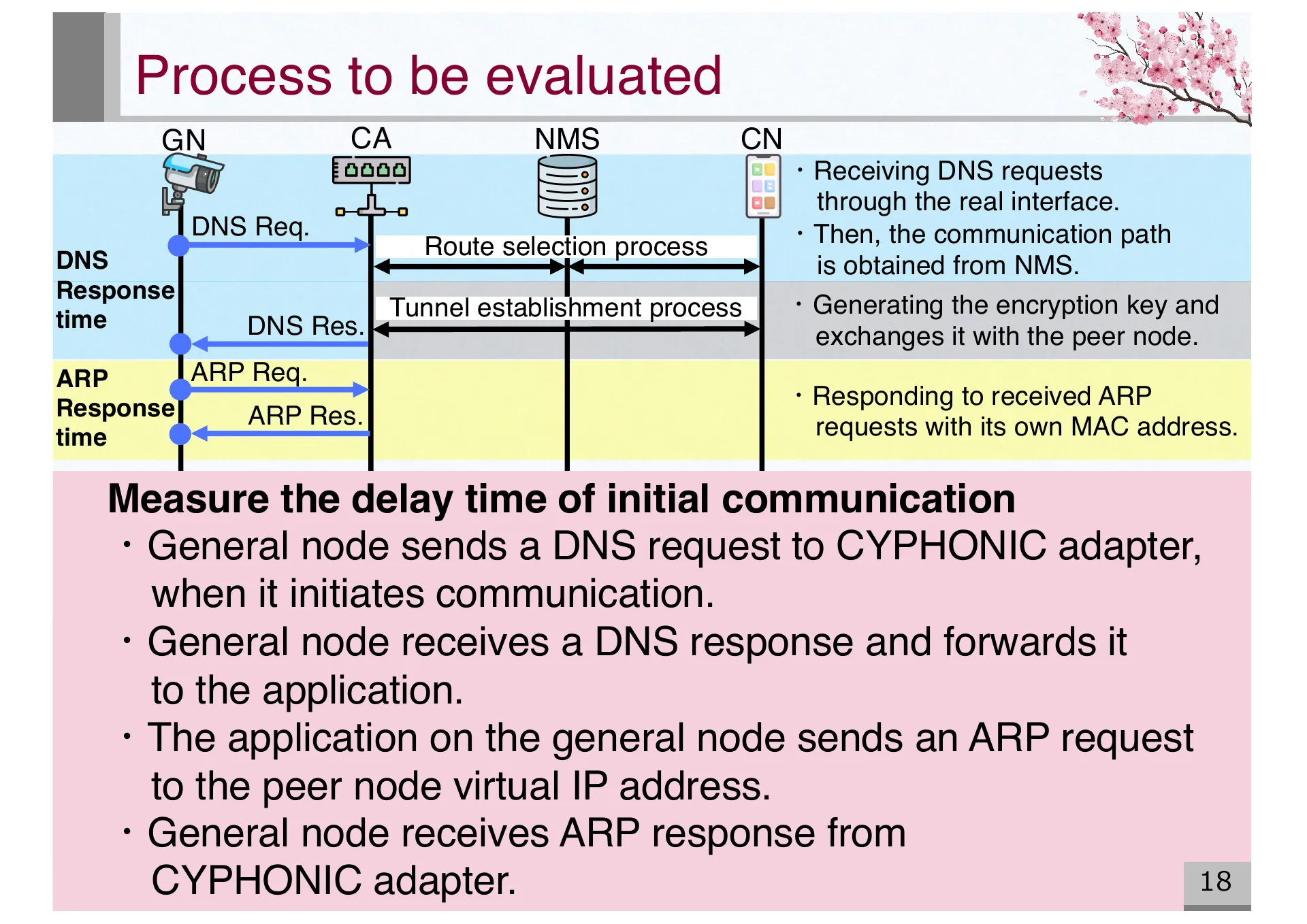
- P.18 — Detailed evaluation process: DNS response time and ARP response time measurement during initial communication
- P.19 — Results of initial communication delay. General node: 28.00ms total. Route selection is the dominant factor in processing time
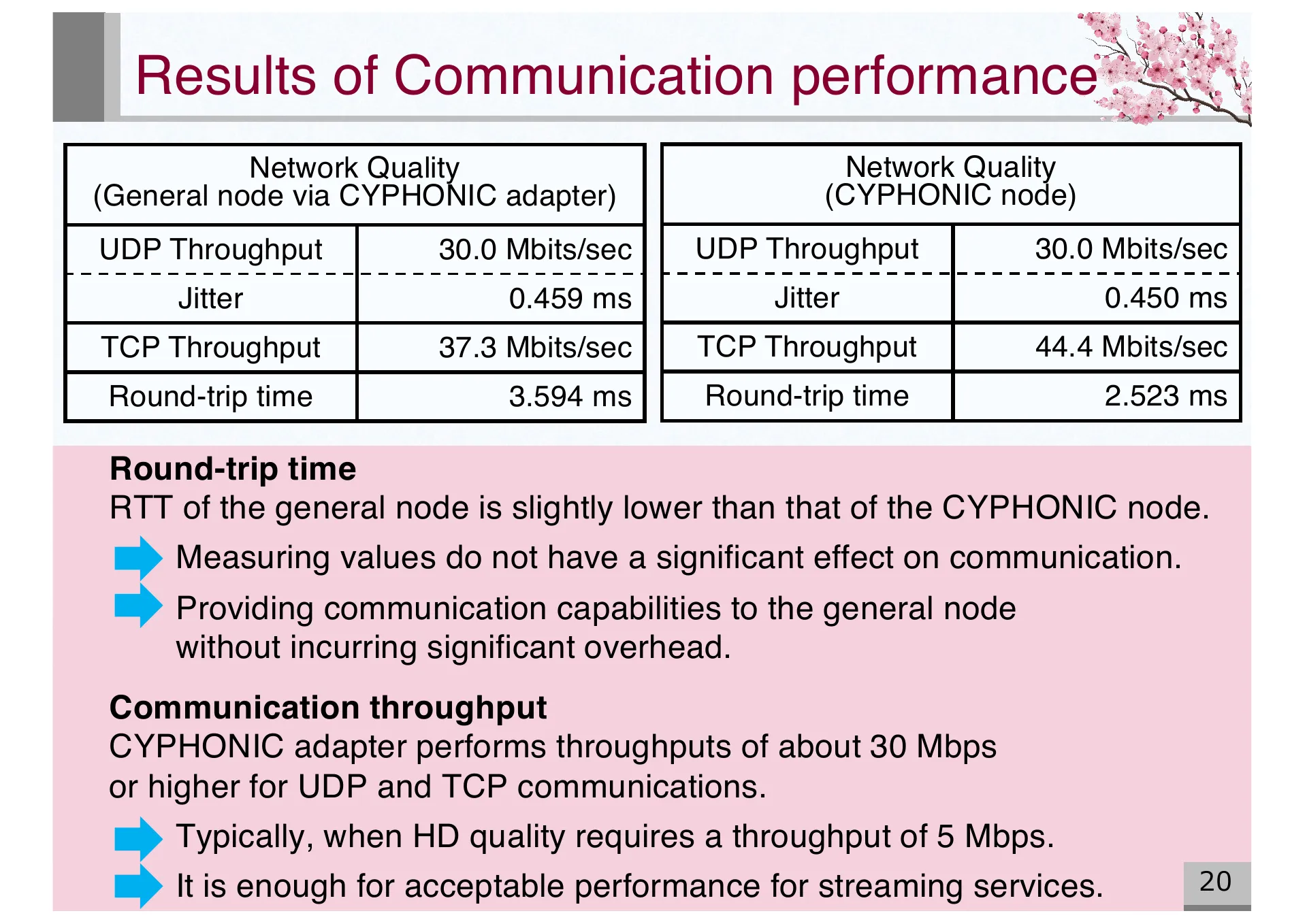
- P.20 — Communication performance results. General node via adapter achieves 30+ Mbps throughput with minimal overhead compared to CYPHONIC node
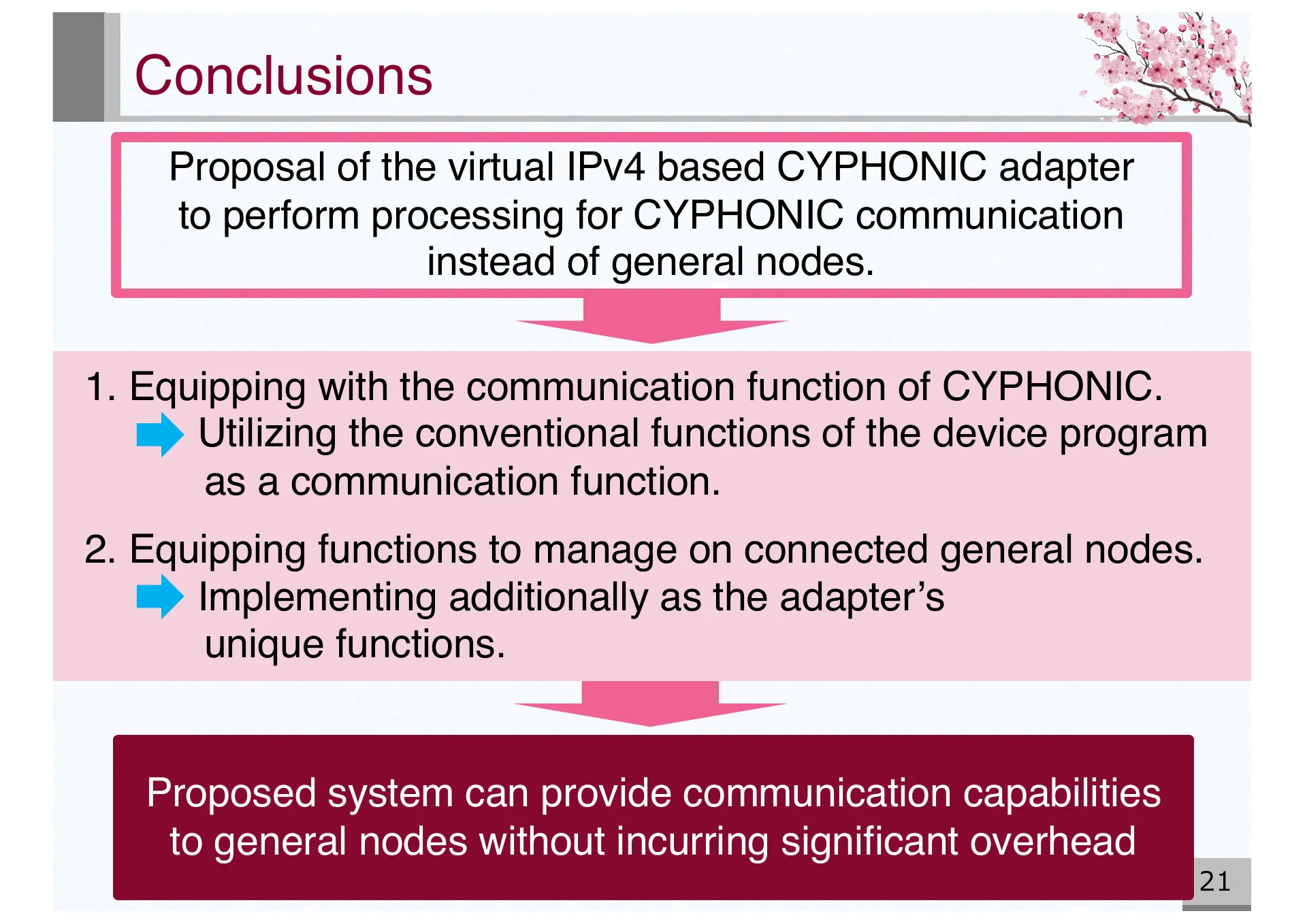
- P.21 — Conclusions. Proposed system provides CYPHONIC communication capabilities to general nodes without significant overhead
- P.22 — Question & Answer slide
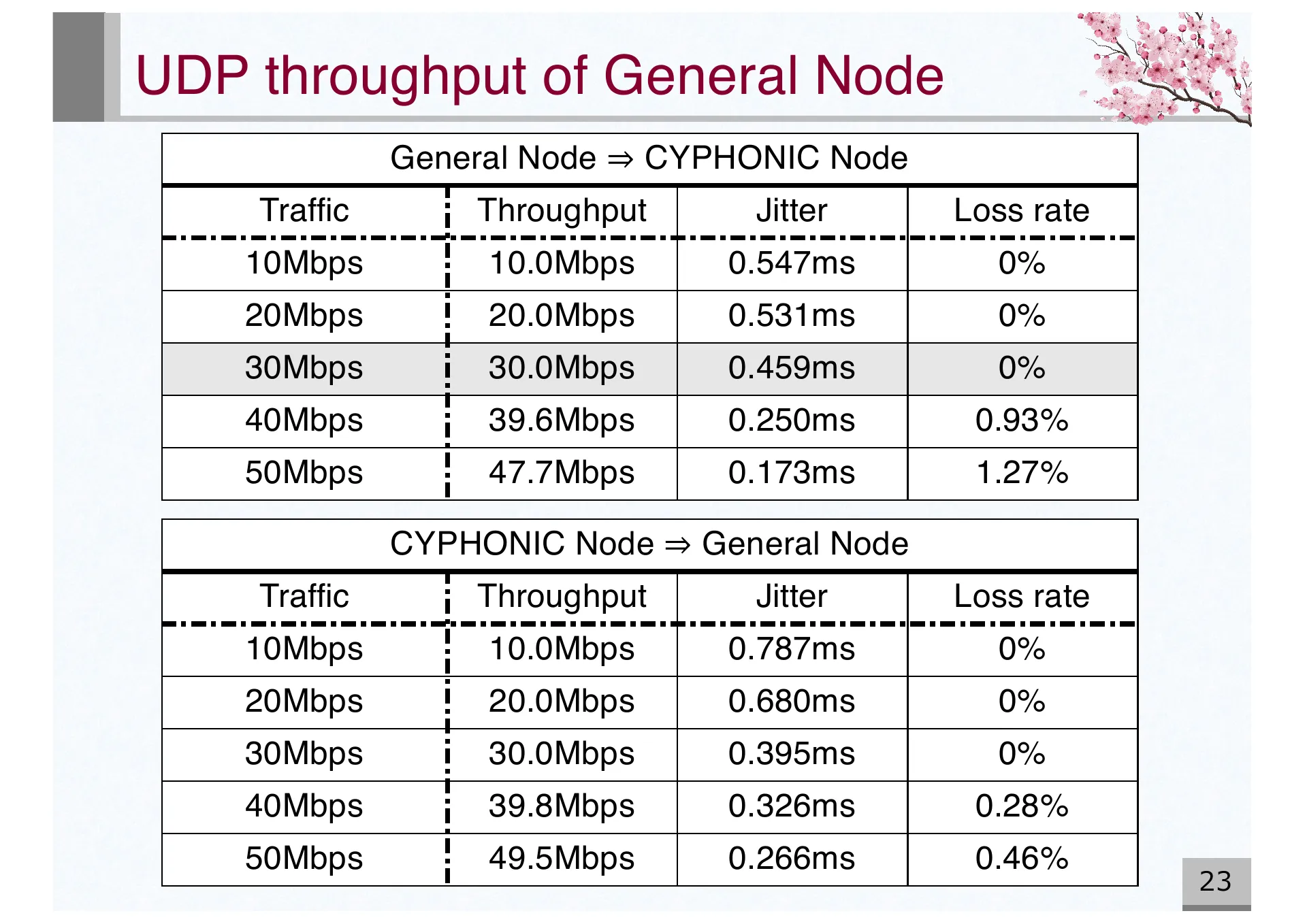
- P.23 — Appendix: UDP throughput of general node. Bidirectional measurements from 10-50 Mbps with loss rate details
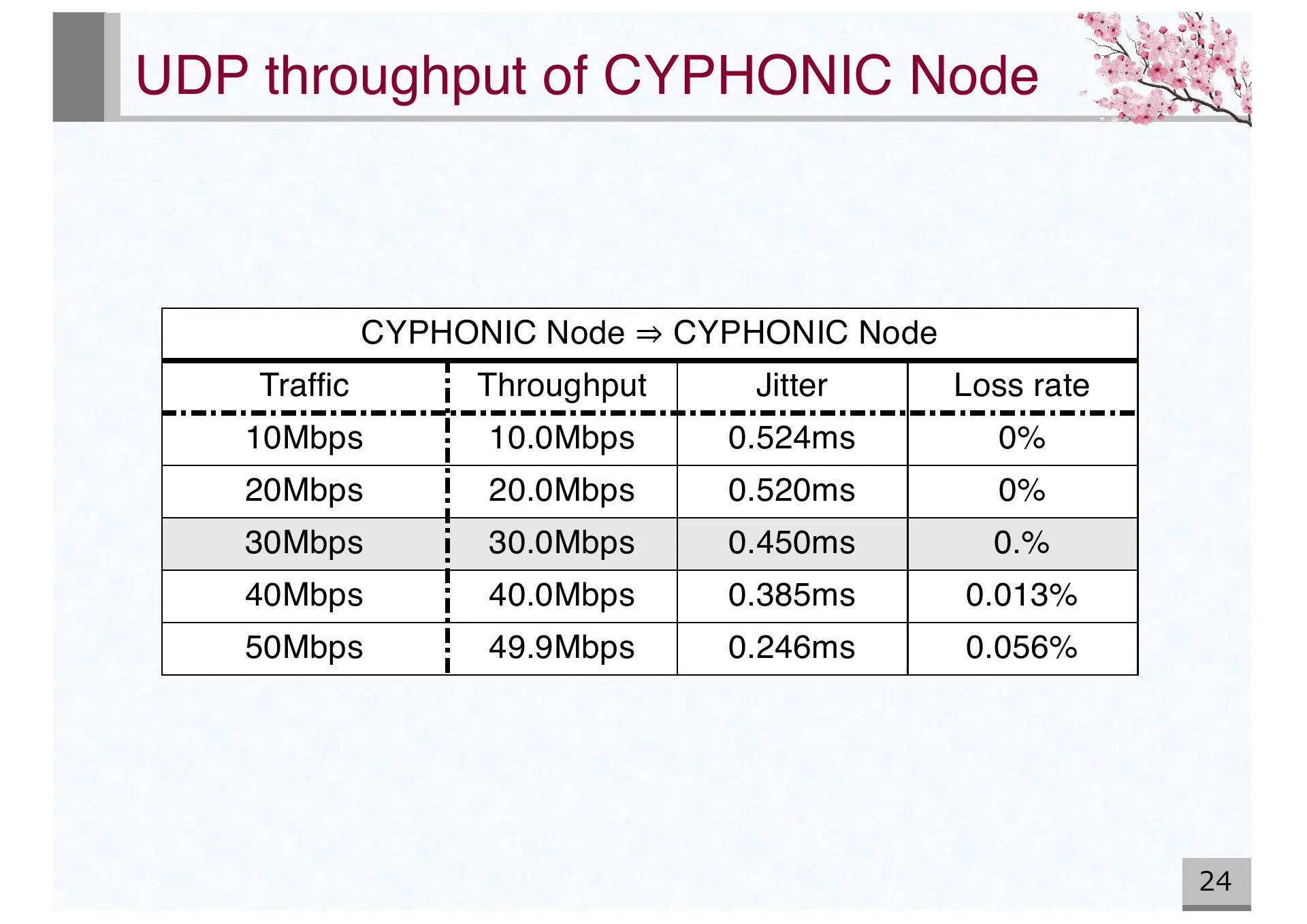
- P.24 — Appendix: UDP throughput of CYPHONIC node. Measurements from 10-50 Mbps showing minimal packet loss
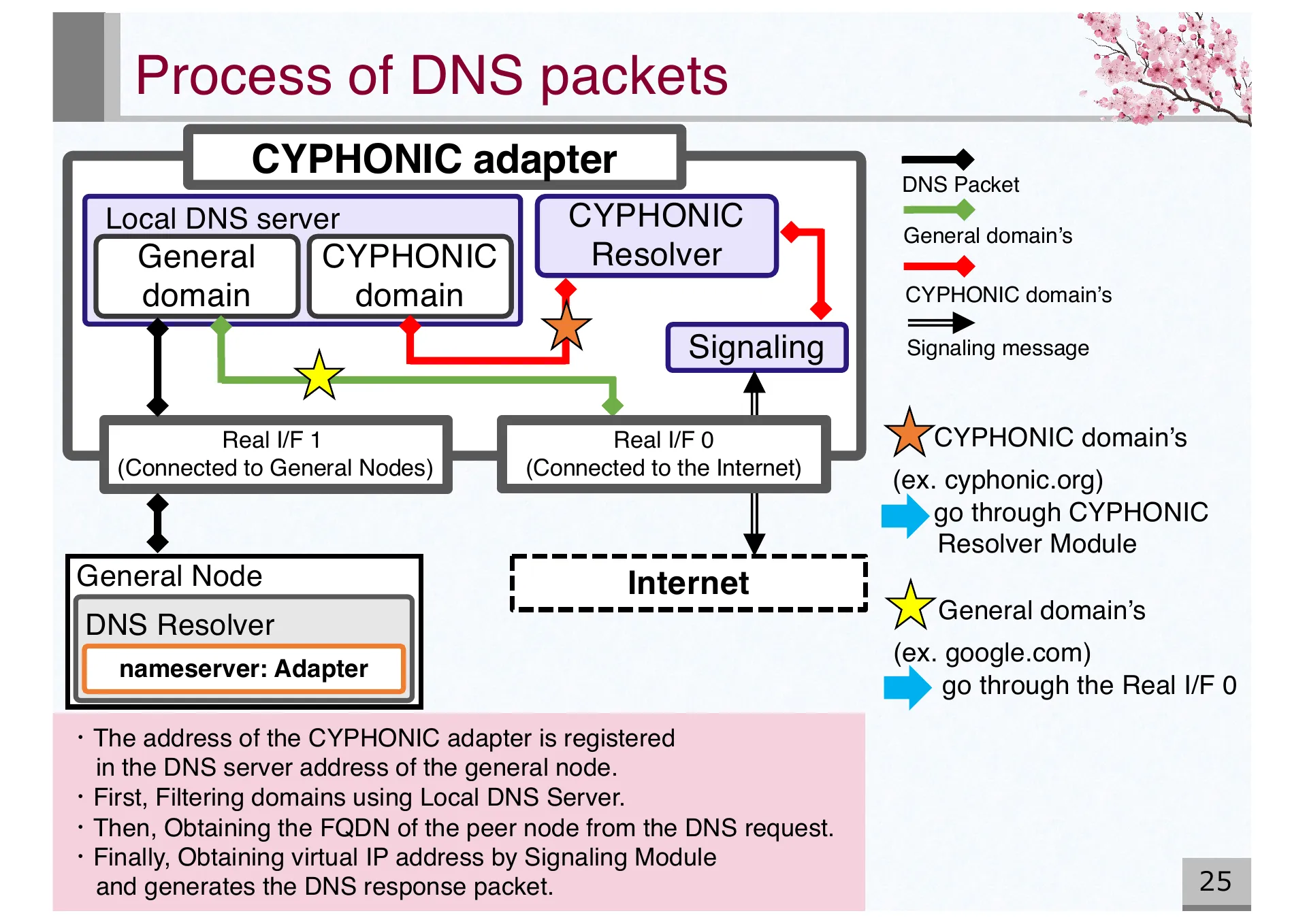
- P.25 — Appendix: DNS packet processing in CYPHONIC adapter. Domain filtering and virtual IP resolution via Local DNS Server and Signaling Module
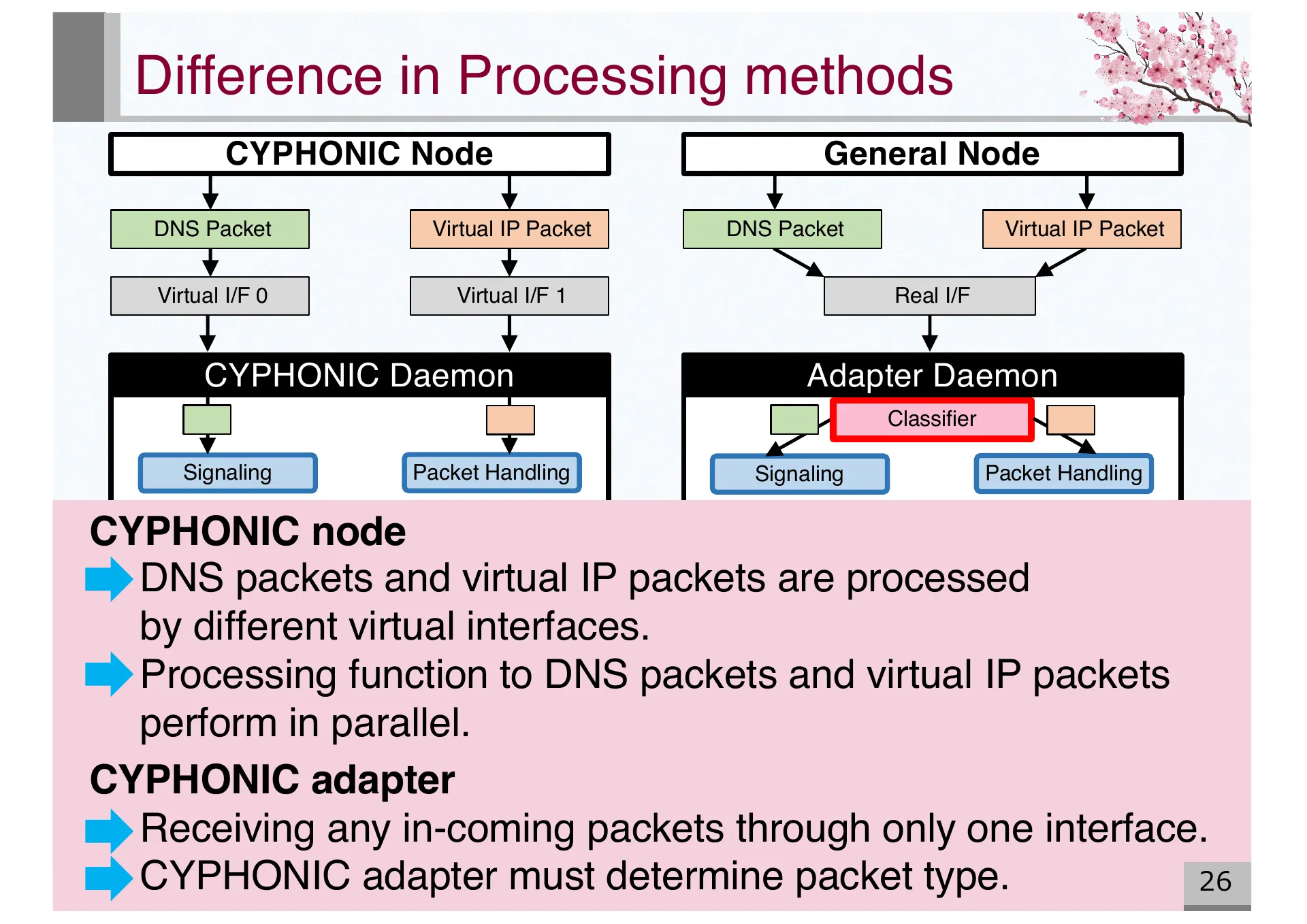
- P.26 — Appendix: Difference in processing methods between CYPHONIC node (dual virtual interfaces) and CYPHONIC adapter (single interface with classifier)
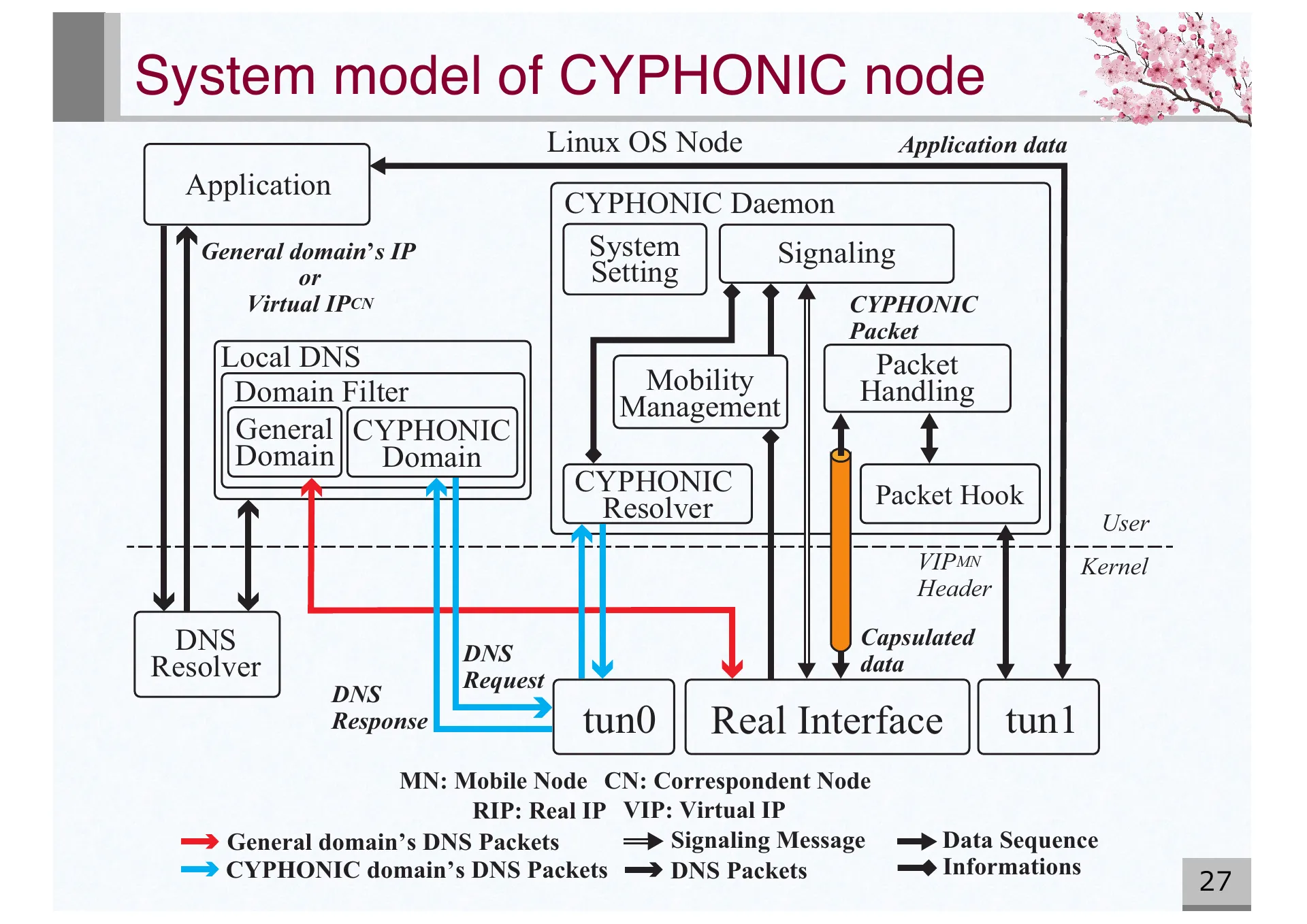
- P.27 — Appendix: Detailed system model of CYPHONIC node showing DNS resolver, domain filter, mobility management, and packet handling
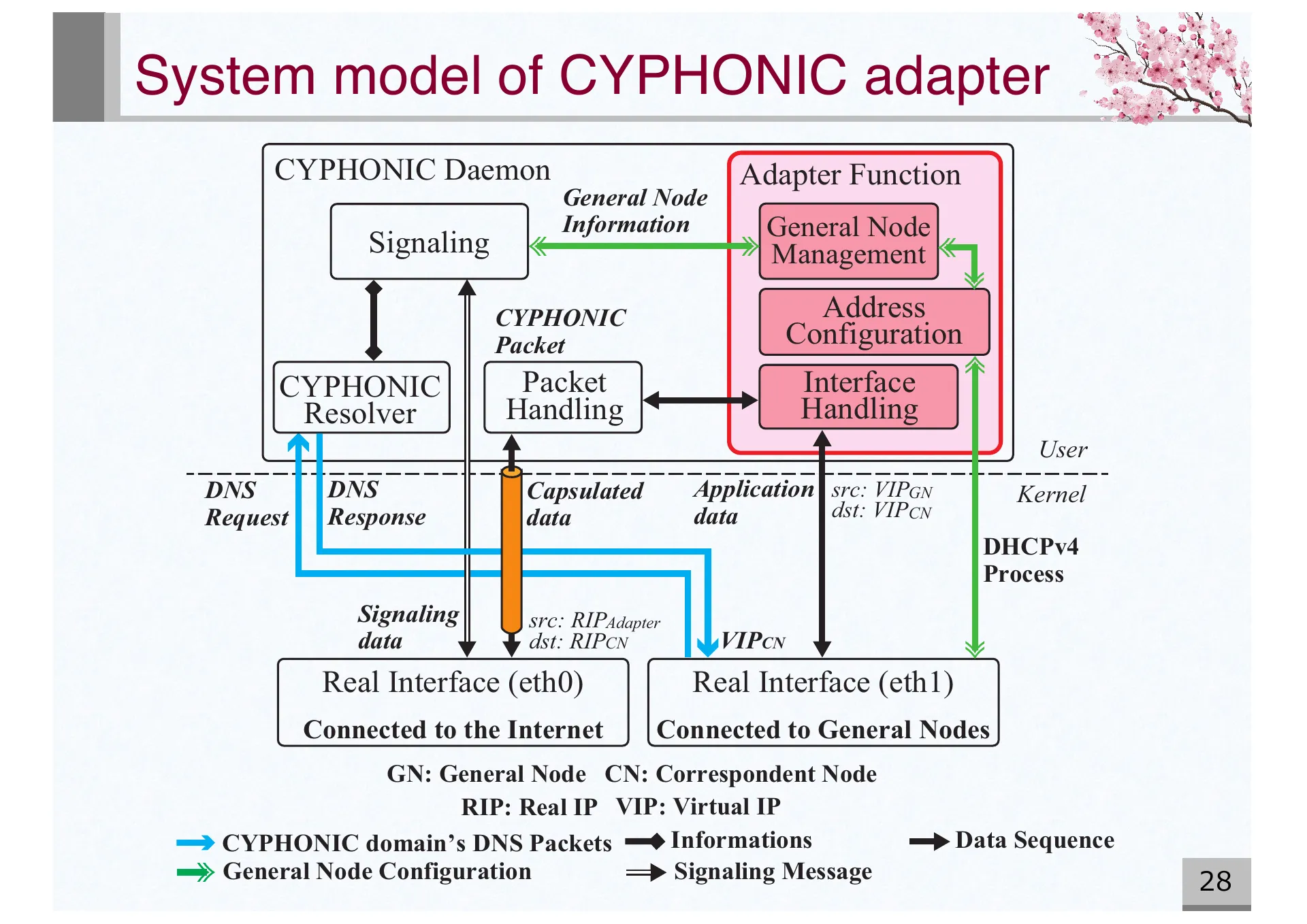
- P.28 — Appendix: Detailed system model of CYPHONIC adapter showing Daemon functions, adapter functions, and dual real interfaces
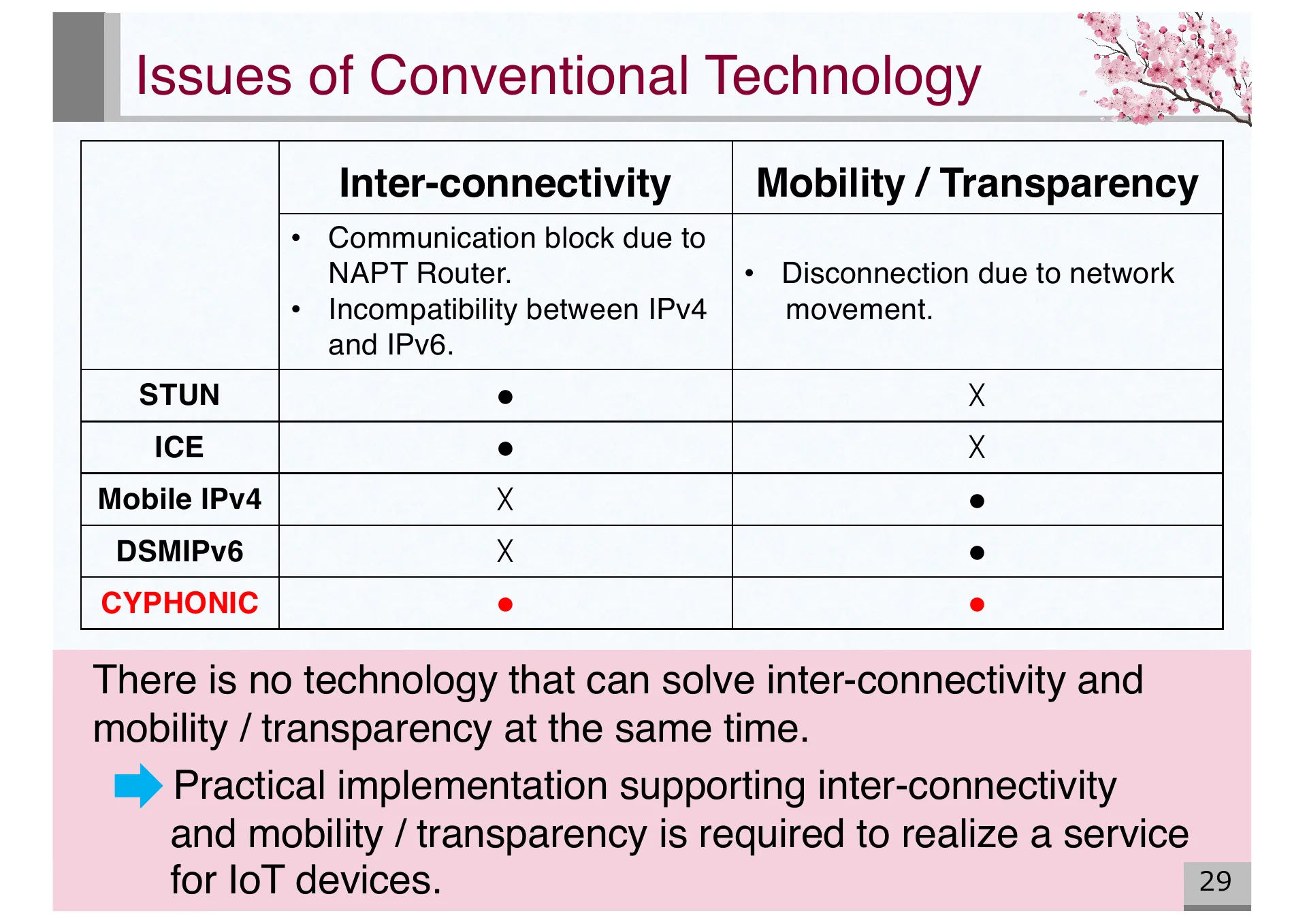
- P.29 — Appendix: Comparison of conventional technologies (STUN, ICE, Mobile IPv4, DSMIPv6) with CYPHONIC for inter-connectivity and mobility
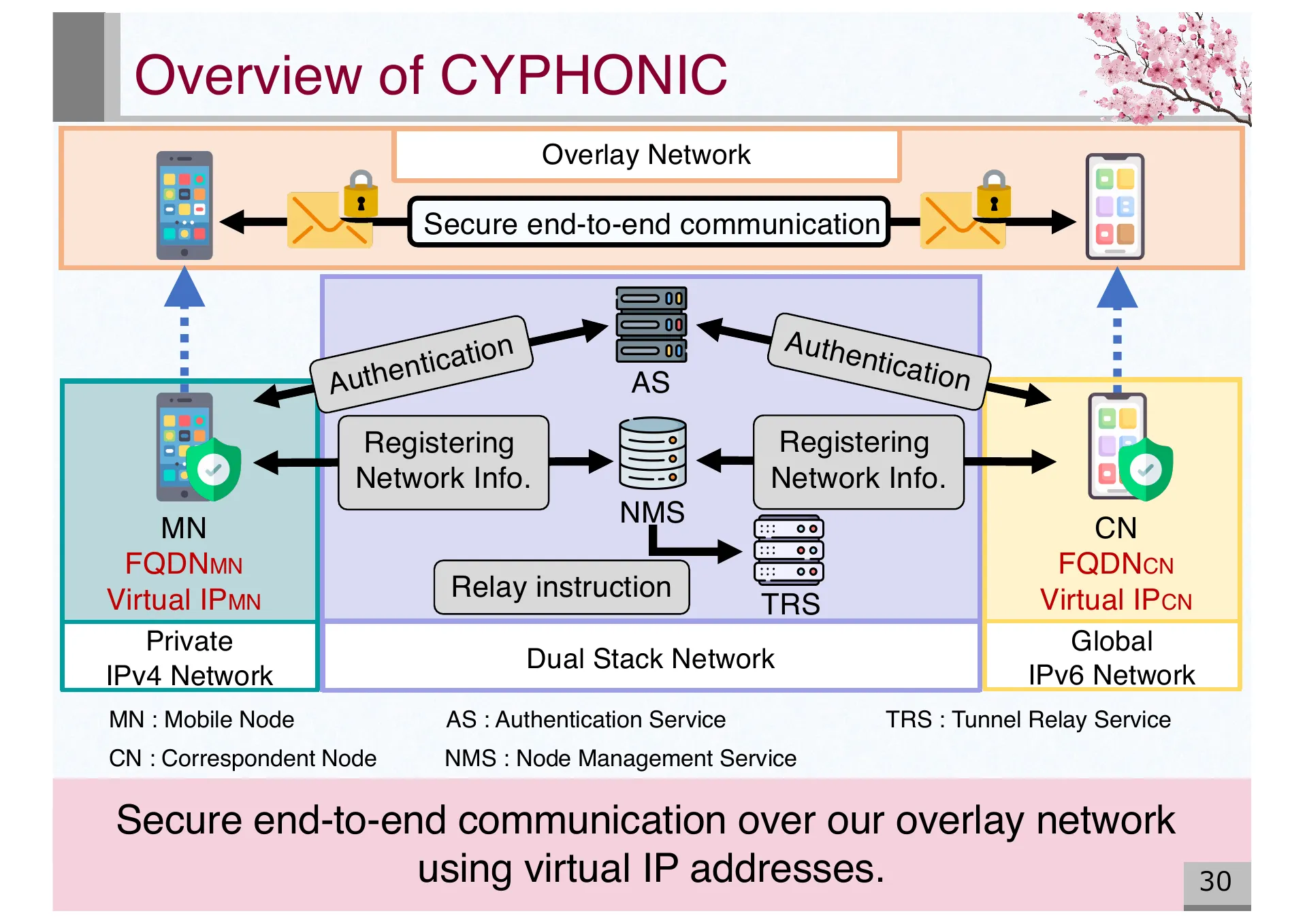
- P.30 — Appendix: Overview of CYPHONIC architecture with AS, NMS, TRS components enabling secure end-to-end communication via overlay network
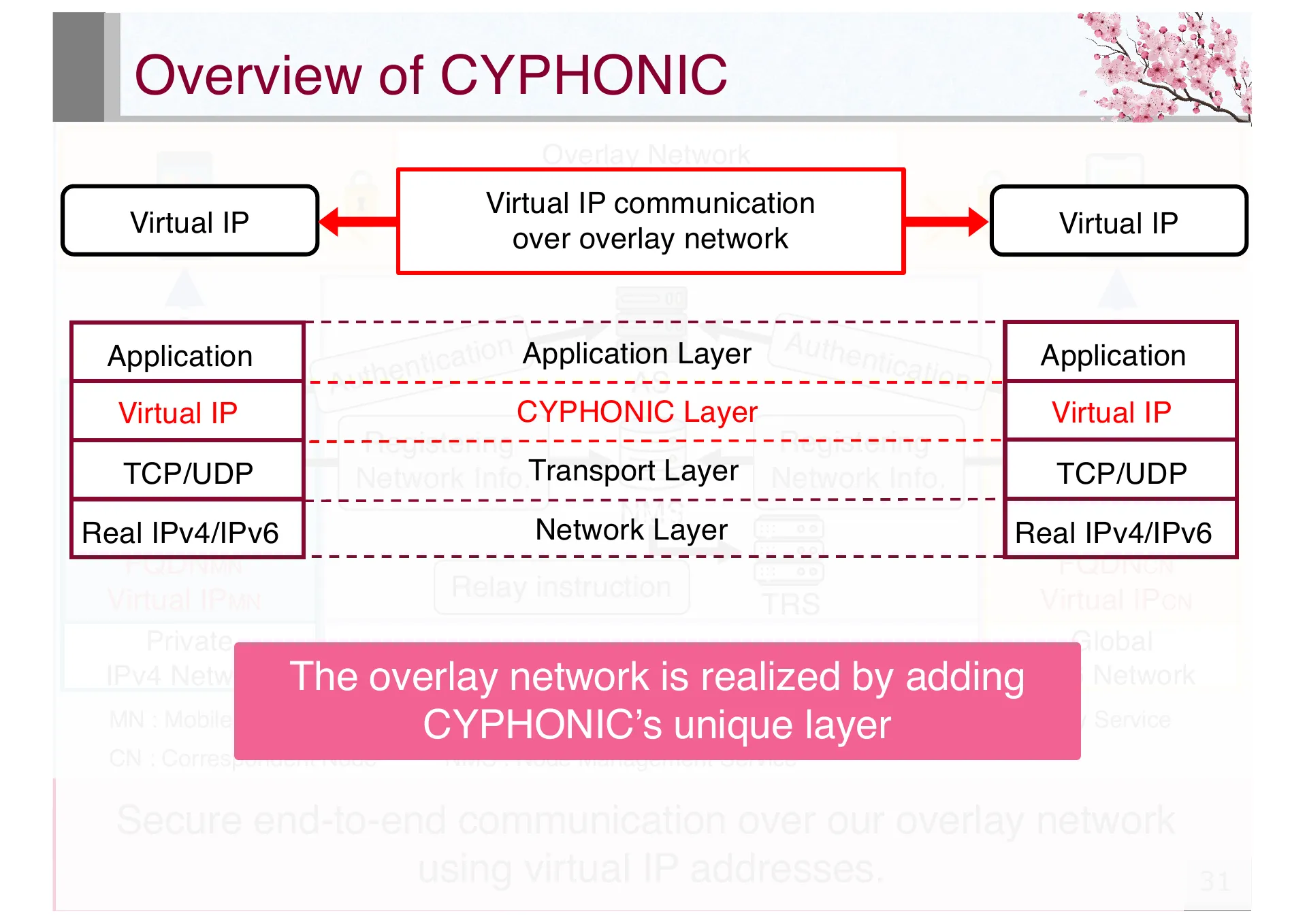
- P.31 — Appendix: CYPHONIC layer model showing how the overlay network adds a unique CYPHONIC layer between transport and network layers
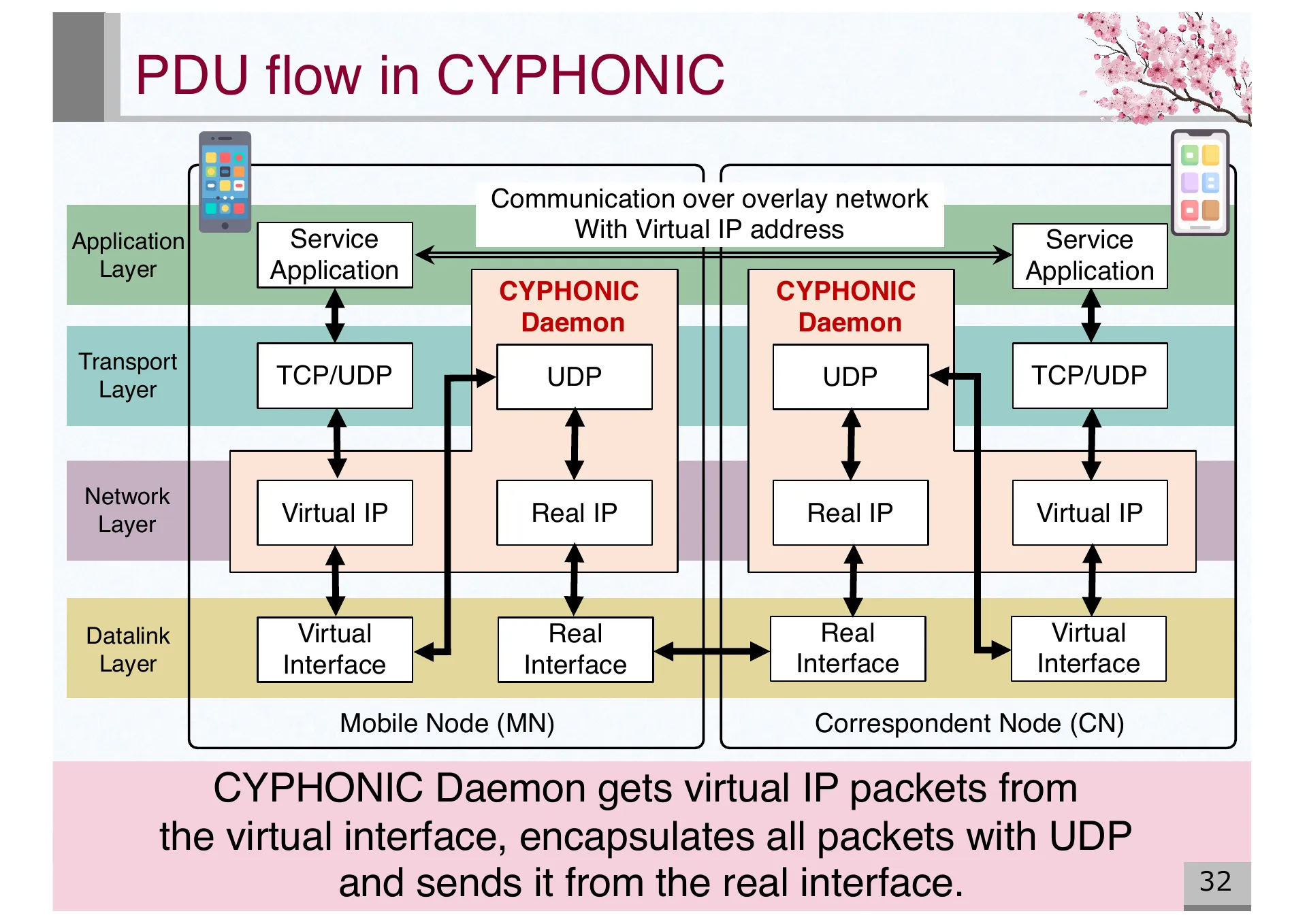
- P.32 — Appendix: PDU flow in CYPHONIC. CYPHONIC Daemon encapsulates virtual IP packets with UDP and sends via real interface
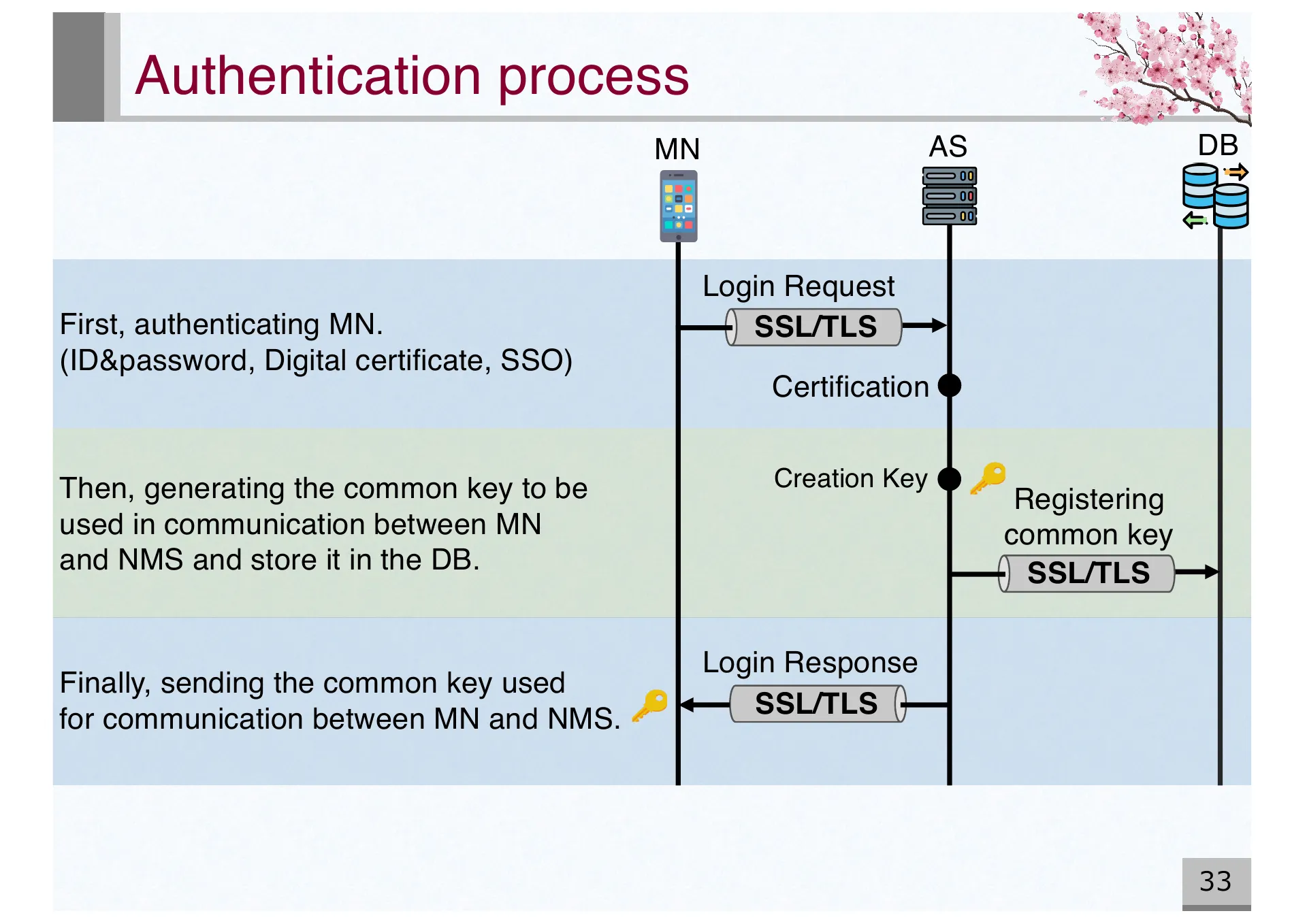
- P.33 — Appendix: Authentication process sequence. MN authenticates with AS via SSL/TLS, generates common key for NMS communication
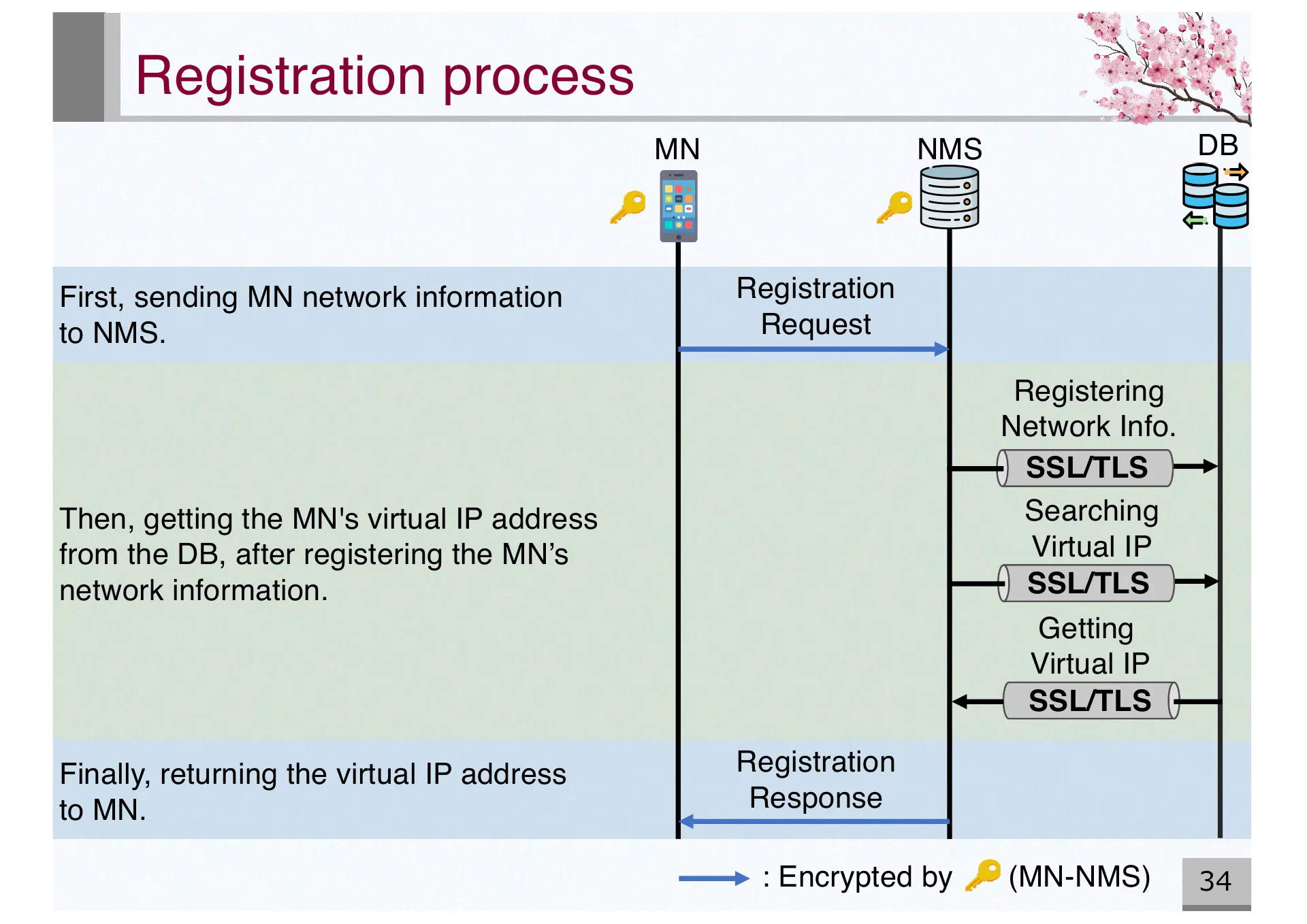
- P.34 — Appendix: Registration process sequence. MN sends network information to NMS and receives virtual IP address
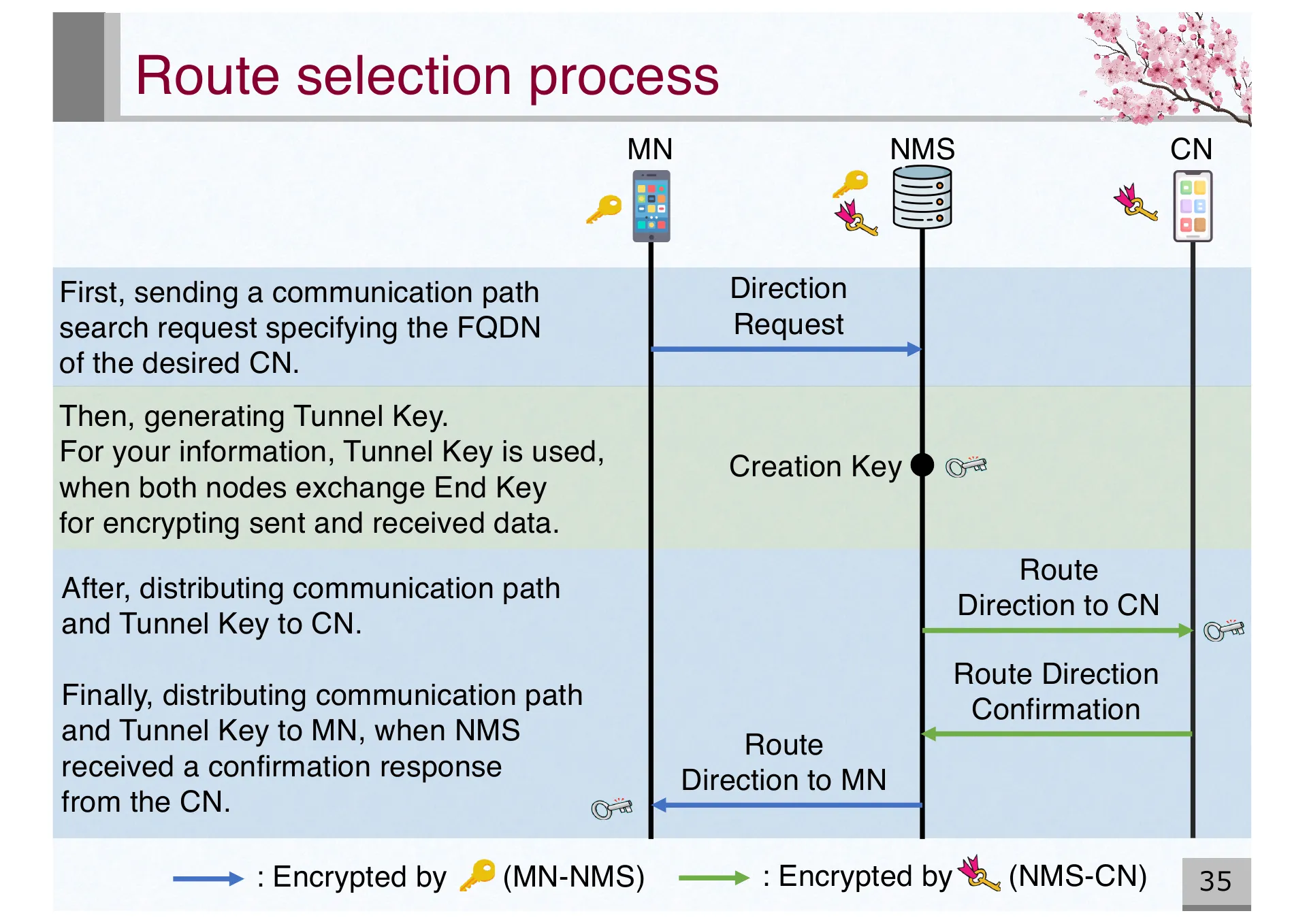
- P.35 — Appendix: Route selection process. MN requests communication path to NMS, which distributes route direction and Tunnel Key to both nodes
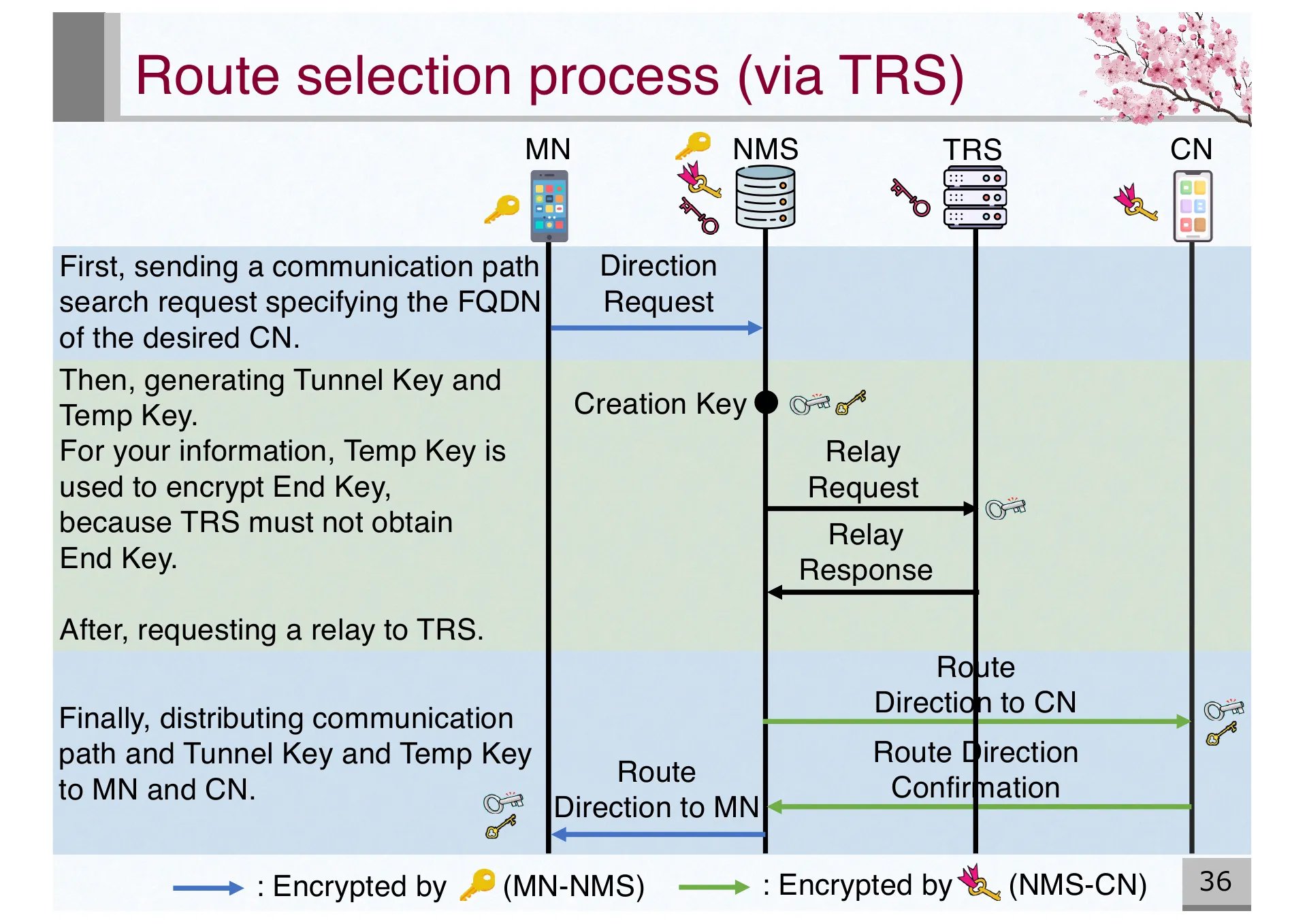
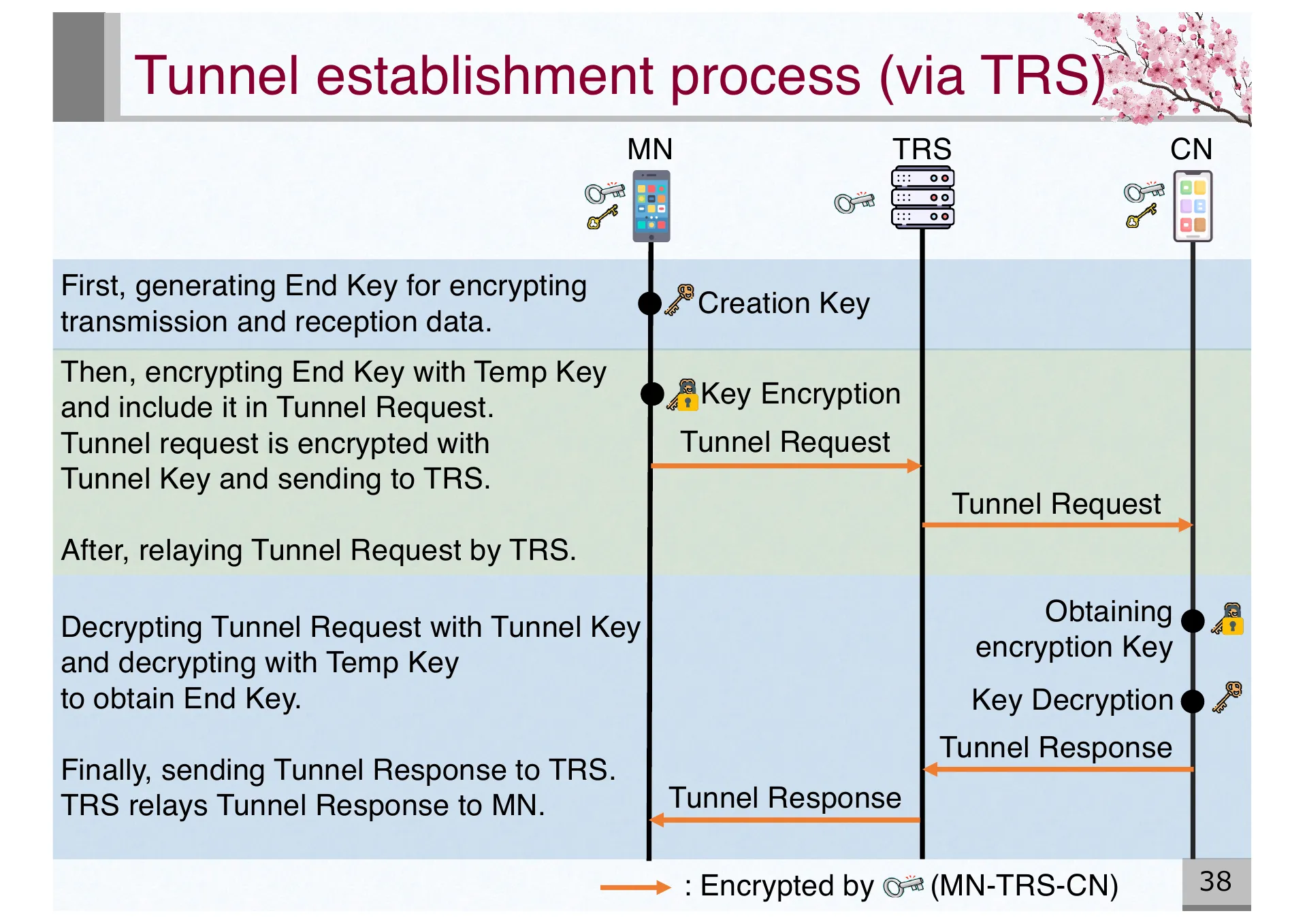
- P.36 — Appendix: Route selection process via TRS. Adds Temp Key mechanism for relay scenarios where TRS must not obtain End Key
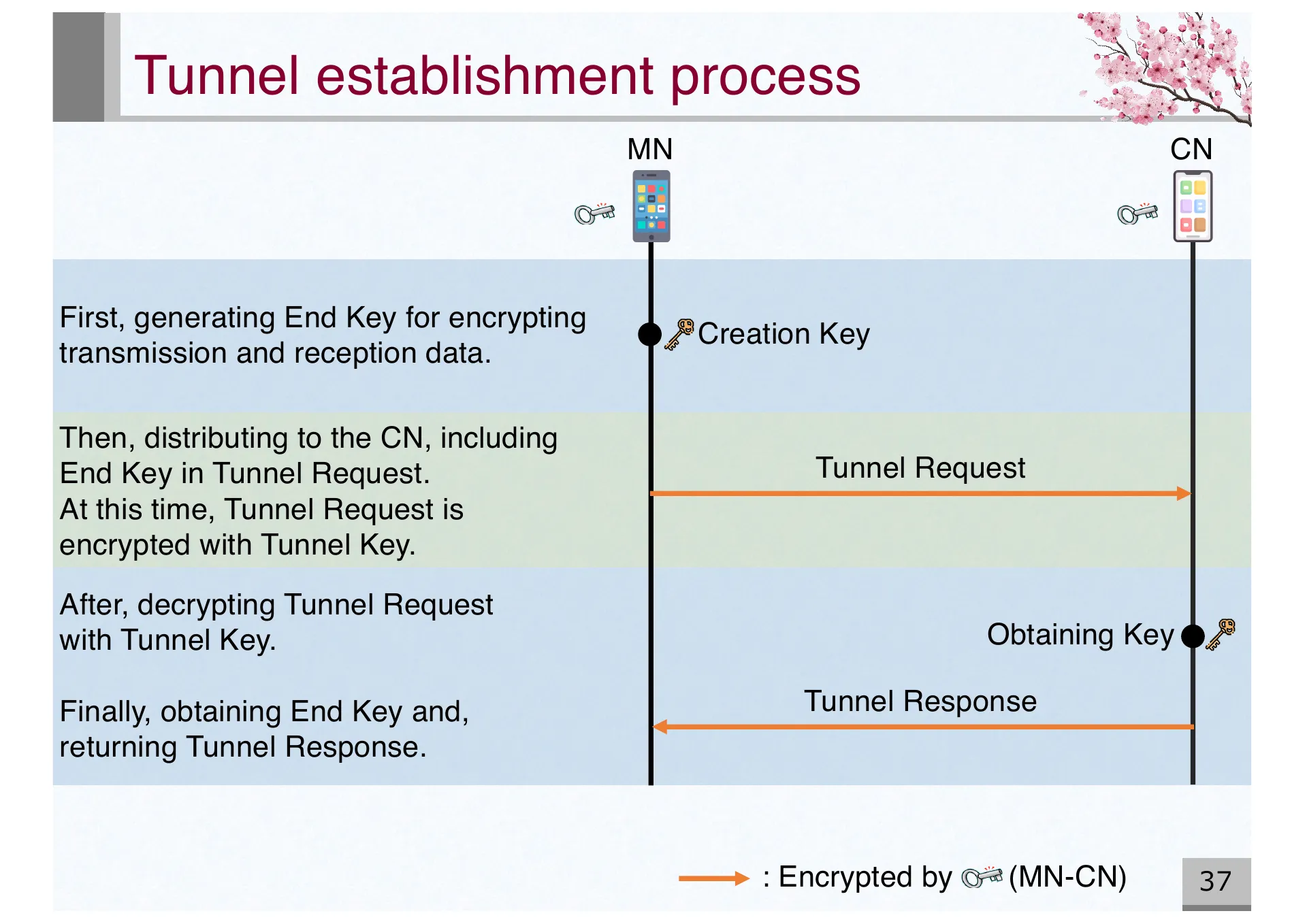
- P.37 — Appendix: Tunnel establishment process. MN generates End Key, exchanges with CN via Tunnel Request/Response encrypted with Tunnel Key
- P.38 — Appendix: Tunnel establishment process via TRS. End Key encrypted with Temp Key to prevent TRS from obtaining it during relay